If you have networking equipment that can support them, setting up virtual local area networks (VLANs) makes sense from a security and management perspective. Your devices will still think they’re on a physical LAN and will be able to talk to each other, but the different VLANs will only be able to talk to each other if you allow it.That’s perfect for keeping insecure IoT devices away from your data, your data away from your guests, and your guests away from the contents of your computer. Unless you decide you want them to talk to each other, of course. It essentially gives you multiple networks from one set of equipment, and makes your life much easier as a budding homelabber or network admin.
6
Inventory your network devices
You can’t manage what you don’t know you have
Before you even set up your first VLAN, the first thing is to take stock of the networked devices in your home. That way, you know what you’re about to manage and can sort them into groups according to whatever metrics you choose.
These could include:
- Laptops
- Mobile devices like phones and handheld gaming consoles
- Desktops
- IoT devices like video doorbells, smart thermostats, and smart lights
- Network-attached storage (NAS) devices
- Servers
- Devices that are regularly at your home but not owned by you
Don’t forget to add your networking equipment to this list because some devices will be unmanaged and need grouping onto VLANs, while some will be managed and creating the VLANs for use by other devices.
Related
10 free and open-source ways to monitor your home network
Know what’s going on in your home network with these solid open-source monitoring tools.
5
Decide on how to group them
VLANs are awesome for keeping essential services accessible but safe
One of the best features of using VLANs is better security, as devices that might be easier to attack can be kept on their own VLAN. Maybe you want to keep all your networked devices that have essential services on their own VLAN, like printers, NAS and other storage devices, and media servers. Keeping your mobile phones on a separate VLAN keeps them connected to the internet while not letting them touch other devices, and keeping laptops or desktops on their own VLAN makes things easier if one gets infected by malware.
However, how you want to group your devices is up to you, and finding the right balance between security and ease of administration is key here. You can even have a demilitarized zone (DMZ) on one VLAN to let web servers and game servers have incoming access from the internet, without opening the rest of your network to a potential attack vector. You’ll still want to run a hardware firewall on your network, but having VLANs correctly configured can slow or stop the spread of attacks if the firewall fails.
4
Don’t forget the guest network
You want to be a hospitable host, but not too hospitable
Access to the internet is almost a human right at this point, and you don’t want to tell your friends they can’t use your Wi-Fi to save their data plan while they’re around. But at the same time, you don’t want to let them access your file servers or your other devices. When you set up a guest network on your router, you’re setting up a VLAN that’s already configured to give devices connected to that network access to the internet while keeping them away from your other networked devices. Your friends get internet access, you stay safer, and everyone is happy.
Related
3
Keep IoT devices segregated
They’re a big security risk and are best kept apart from your other devices
When adding Internet of Things (IoT) devices to your network, keeping them away from your other networked devices is always a good idea. It’s not that they’re inherently insecure, but they tend to be quickly designed and rarely updated when security fixes for the hardware inside arrive, so they could be a potential issue.
When adding Internet of Things (IoT) devices to your network, keeping them away from your other networked devices is always a good idea.
The easiest way to keep them, and you, safe is to put all of your IoT devices on their own VLAN, with limited or no access to the internet. This might limit some of their functionality if you’re able to access them from outside your home, but you can put those on their own VLAN and ones that don’t need access to the wider internet on a second VLAN. That limits the exposure of your data-containing devices if one of the IoT devices gets hacked and also stops them from intercepting network traffic between your private devices.

Related
4 reasons you should use your SBC as an IoT hub for your smart home devices
Despite their small stature, SBCs are great for monitoring and controlling your smart gadgets
2
Custom firewall rules
Which VLANs can talk to each other and which can’t
Now you’ve got your devices on their own VLANs; it’s time to decide which devices need to be able to talk to those on other VLANs. This could be as simple as letting your laptops and desktops talk to your NAS to transfer data, or your streaming boxes to your home media server. Maybe you’ve got a printer and other networked devices on one VLAN that you want every one of your computers to be able to access or you want to be able to see your video doorbell from your laptop.
With VLANs set up, a managed switch, or a suitable router, you can then set custom firewall rules to get those devices and only those devices talking to each other. This is fantastic for controlling the flow of data around your network, building skills you could use in the workplace, and keeping your homelab in a place that it can’t affect the rest of your network if it goes down.
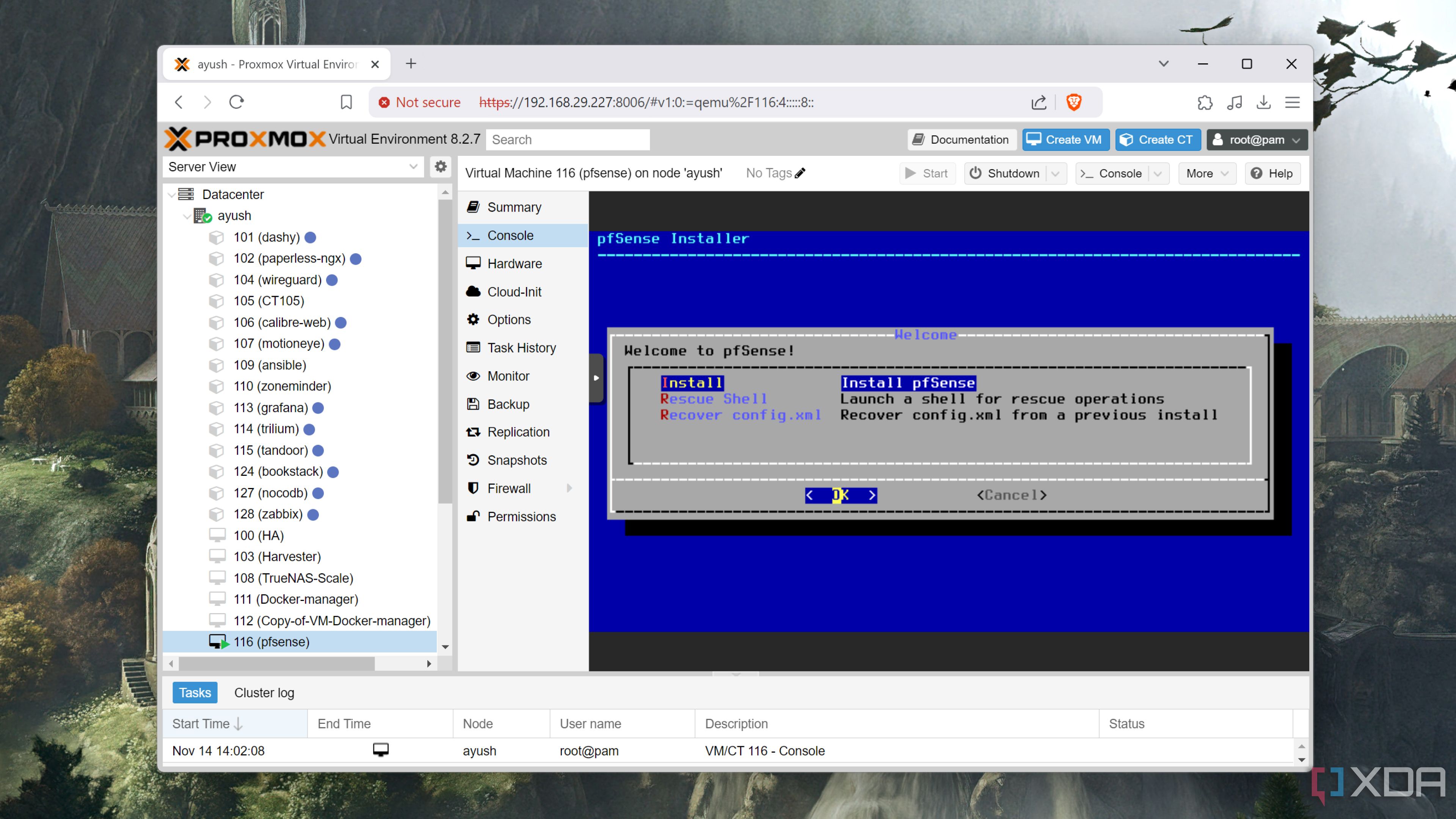
Related
You can virtualize your router and firewall – here’s how
Virtualizing a router isn’t anywhere nearly as difficult as you might think, provided you’ve got some spare network interfaces
1
Managed switches are more expensive
The more you want to do with them, the more you’ll have to pay
While simple, unmanaged switches can be relatively inexpensive, they can’t set up VLANs or let you configure any settings. Managed switches give you more utility, but the price increases with the number of additional features. If you’re going to be using VLANs on your network, you’ll want a managed switch with many ports so you can do advanced things like put individual VLANs to specific ports. You could even take this further and have that port go to another switch to expand the VLAN to more devices, but that one doesn’t have to be a managed switch if you don’t want it to be.

Related
9 things you can do with a managed network switch
We take a look at the great features that a managed network switch can provide, and why they are so important.
VLANs are amazing, but they take some thinking before you put them into practice
You don’t have to manage a huge corporate network to find utility in using VLANs. They’re an essential part of advanced network management and help keep your home network safer. There’s even the chance your router already has one in the inbuilt Guest Network feature, so you can still set one up to put less secure devices on even if you don’t have a prosumer router.

Related
How to easily replace your ISP router with a custom OPNsense firewall
Easily create your own router with this free open-source software
#setting #VLANs #home #network
source: https://www.xda-developers.com/things-you-need-to-know-before-setting-up-vlans-on-your-home-network/







