When you finally get tired of your ISP router, one of the most-recommended replacements is making your own with a custom OPNsense firewall. This puts the power back in your hands, limits what your ISP can do to your connection, and gives you plenty of protection and features you’ve been missing all this time. But one of the awesome things about OPNsense isn’t just that it’s a powerful router, but that you can make it even better by installing other services as plugins. While there are plenty to go through, some of them I consider essential, and that’s the ones here.
Related
6 best practices for deploying pfSense or OPNsense in your home lab
Home lab life is all about learning, and already-established best practices will help your journey.
6
Zenarmor
One of the best IDS/IPS systems to keep your network safe
The internet was always a scary place, but it’s even more so nowadays with the prevalence of state-sponsored hacking groups, automated port scanning systems, and who knows what malware and worms waiting to get into your systems. OPNsense does a good job of protecting your home network with the default configuration, but adding an IDS/IPS system is the first thing I always install.
Zenarmor might not be free, but there’s something to be said about paying for your security software and knowing it’s being maintained properly. It basically monitors your network, alerts you if there’s unusual traffic, and can even spot emerging threats and block them before you have to get involved. Zenarmor in “protect” mode sometimes drops friendly traffic that’s behaving strangely, but if so, it’s easy to allow that traffic so that the protection system knows it’s okay to be on your network.
It can block malware, phishing sites, spam, botnets, spyware, and more, and it’s got a nice dashboard for changing settings and viewing the things it monitors or blocks. Plus it’ll show you DNS requests and more, so that you get a sense of what’s going on inside your network from the micro view all the way to the macro.

Related
I turned my Ugreen NAS into an OPNsense router for my home, and it works perfectly
The Ugreen DXP4800 Plus NAS has some great hardware, and it’s perfect for OPNsense.
5
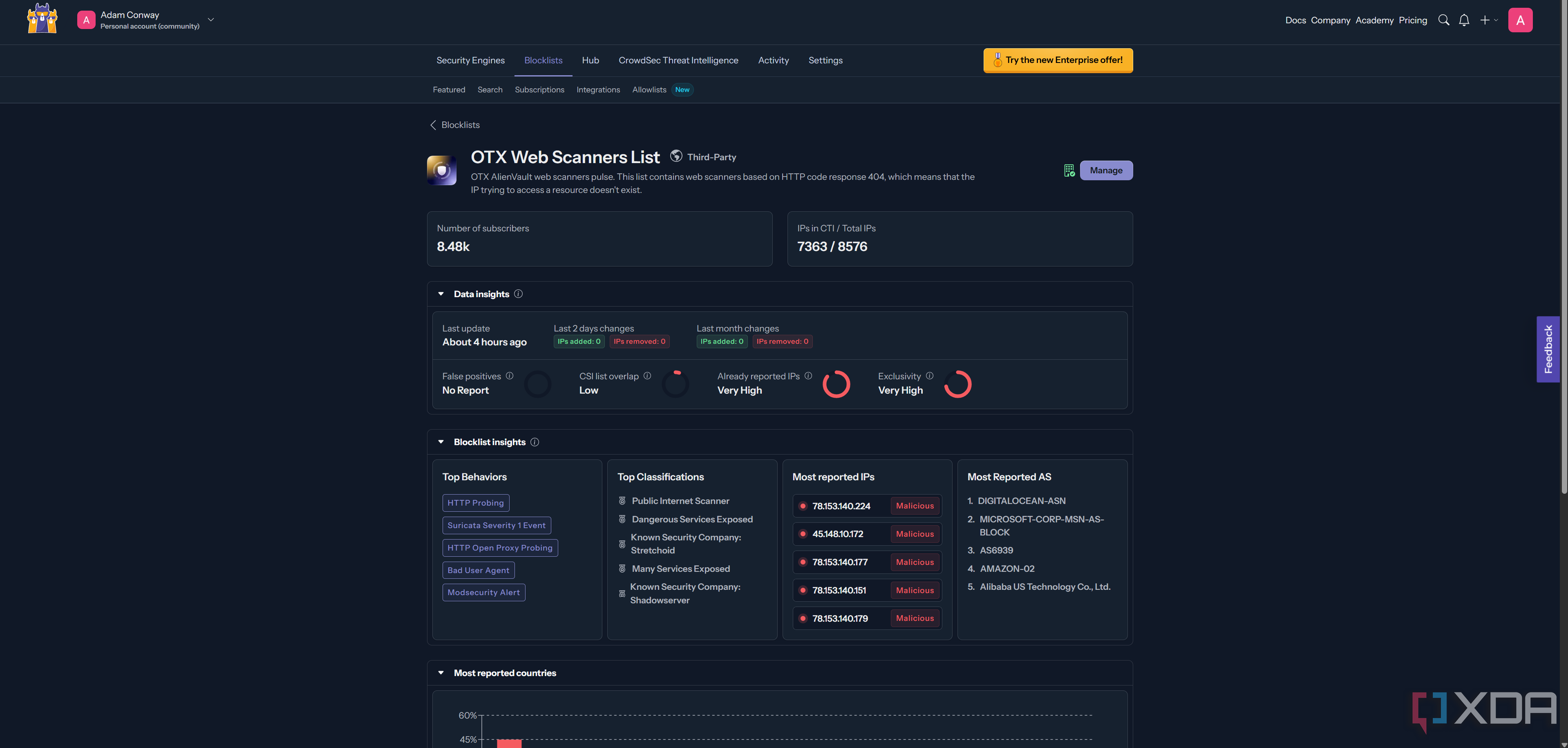
CrowdSec
Keep known threats from connecting to your IP address and scanning it
While it’s excellent that IDS/IPS systems can alert you once threats are on your network, it’s always better to block them at the source before they can access anything. That’s where CrowdSec comes in, as it stops known threat IPs from even trying to connect to yours. Think of it as a crowdsourced bouncer for your home network, that proactively kicks out known troublemakers before they can start a ruckus. It’s fantastic, and because it drops traffic before it gets to your network, it also reduces noise so that any issues stick out better as you’re not sifting through even more data.

Related
I set up intrusion detection and intrusion prevention on my network using OPNsense, here’s how
It’s been working great, and I really recommend setting it up yourself.
4
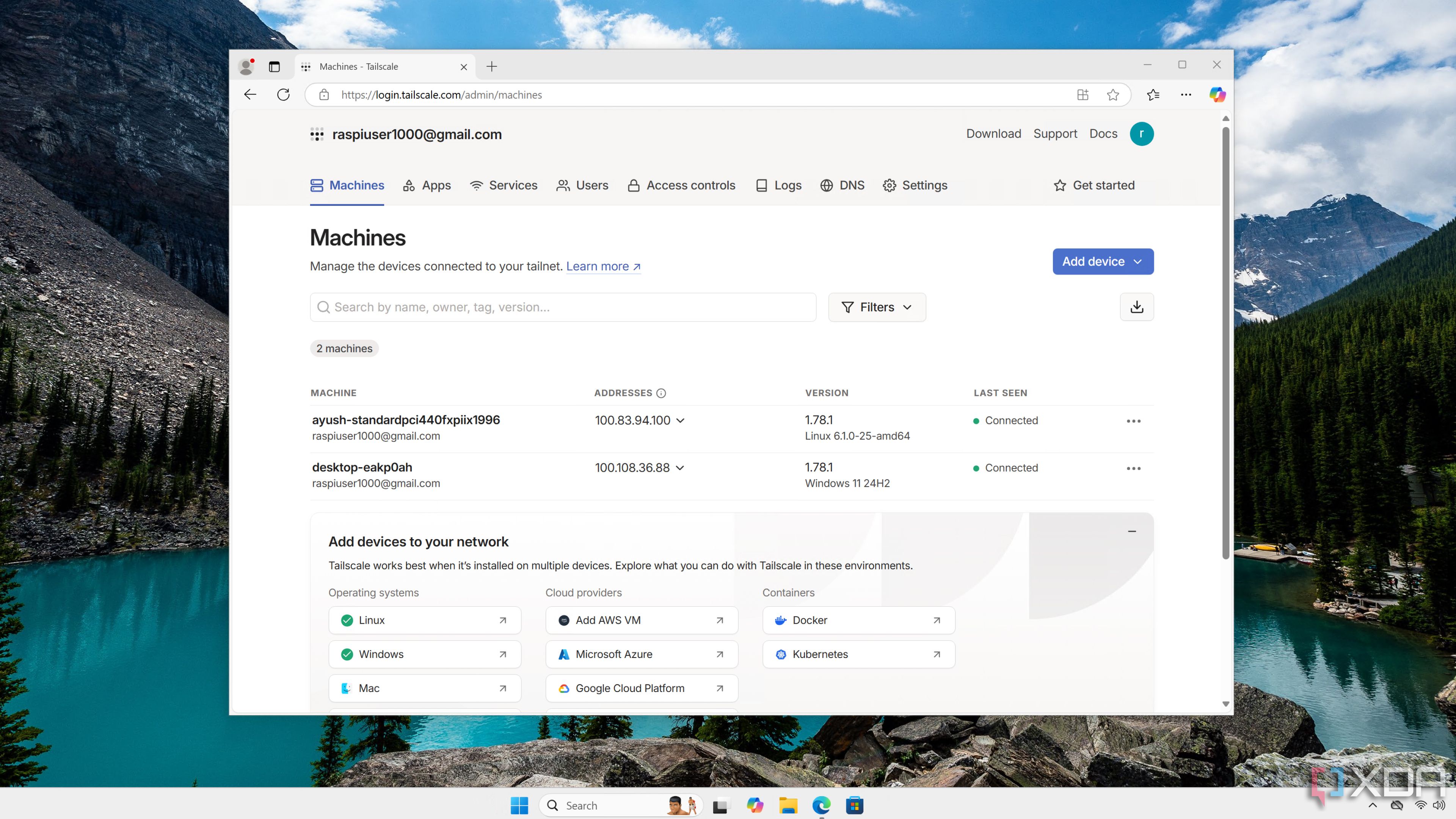
Tailscale
My favorite remote access tool is easy to set up and use
While I’ve tried plenty of remote access tools for my home lab, I keep coming back to Tailscale. It takes the pain out of remote access, doing all the VPN connection setup stuff I absolutely abhor automatically, so that I can focus on using my self-hosted tools. It’s built on WireGuard so it’s already secure, my Tailnet works no matter where my devices are, and I can use SSO to sign in and authenticate so I don’t have to worry about always-on connections. Plus, it sidesteps the annoying NAT issues that my residential fiber connection experiences, so I don’t have to keep ports open all the time to use it.
Related
I use Tailscale to remotely access my self-hosted services – here’s how
Tailscale provides an easy way to access your home server from external networks
3
Nginx
It might not be the best reverse proxy currently, but it’s the one I best know how to use
While OPNsense has plugins for HAProxy, Caddy, postfix, relayd, and ftp-proxy, I still prefer to use Nginx. Old habits die hard, I guess, but you can use one of the other reverse proxy solutions if you prefer. I’m used to it now and know what I’m getting into each time I change DNS records, and it’s powerful enough for what I need, which is mostly connecting to self-hosted Docker containers by nicely readable URLs instead of having to remember IP addresses and port numbers.
It might not be as fast as HAProxy, or able to pull its own self-signed certs like Caddy, but Nginx is still used by a huge swathe of industry, making it easy for me to find tutorials to fix things when, invariably, they go wrong.

Related
Reverse proxies are incredibly handy in the home lab, and Nginx is one of the best known.
2
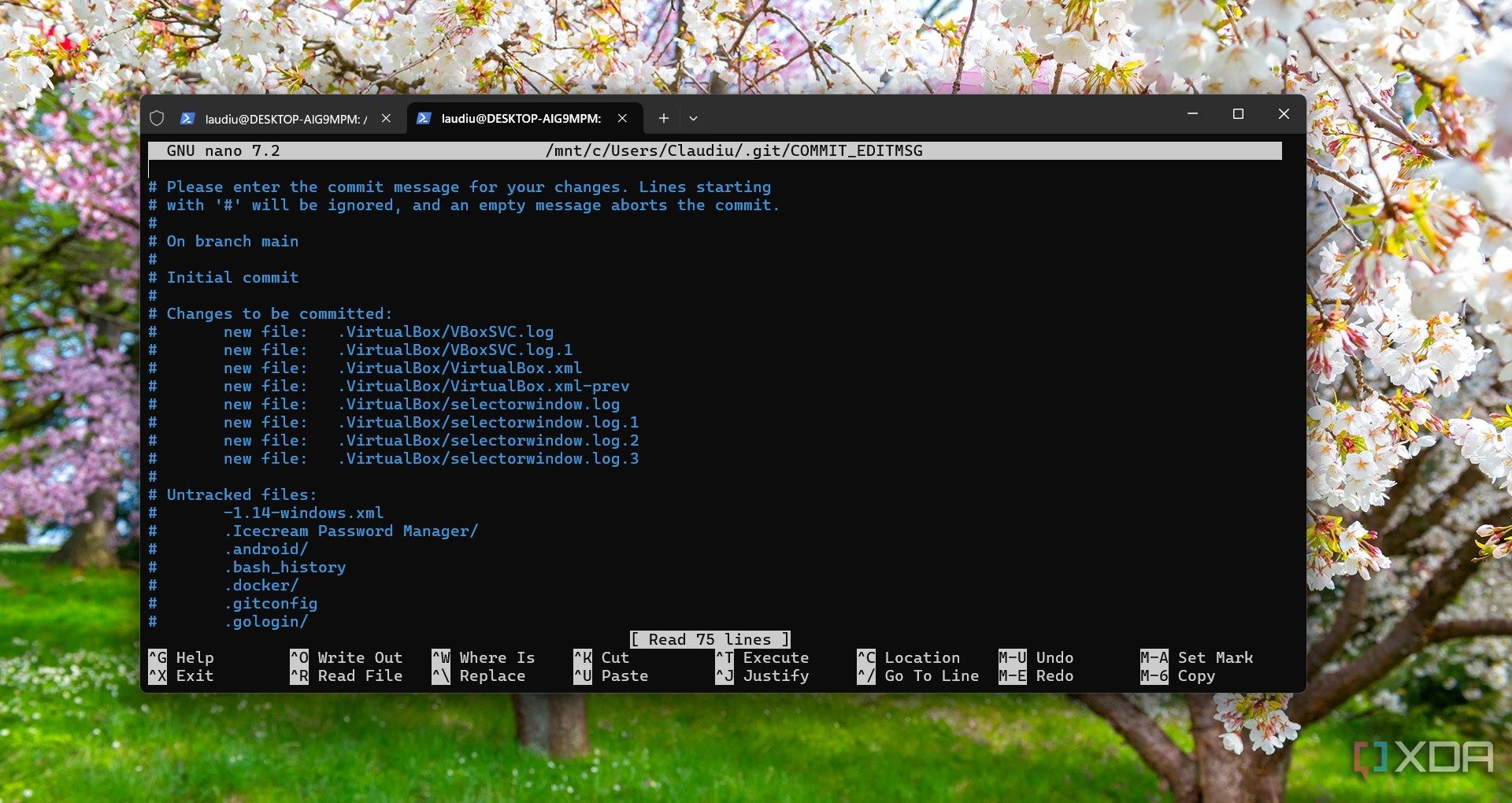
os-git-backup
Keeps my configuration changes backed up to Git
We love documentation of our home lab procedures, and it’s even better when you can outsource that to an automated tool. This fantastic plugin keeps traceability of any changes to your OPNsense firewall by writing configuration changes to Git, so you have a complete record of what’s done, no matter which user is logged in. That way, you can easily revert any troublesome issues, as you know exactly what you’re looking for. It’s also handy for keeping backups of your configuration in case you need to wipe your router’s drive, and you can be back up and running in minutes.

Related
4 reasons you need to run a Git server on your NAS (even if you’re not a developer)
If you’re looking for your next NAS project, you need to set up a Git server.
1
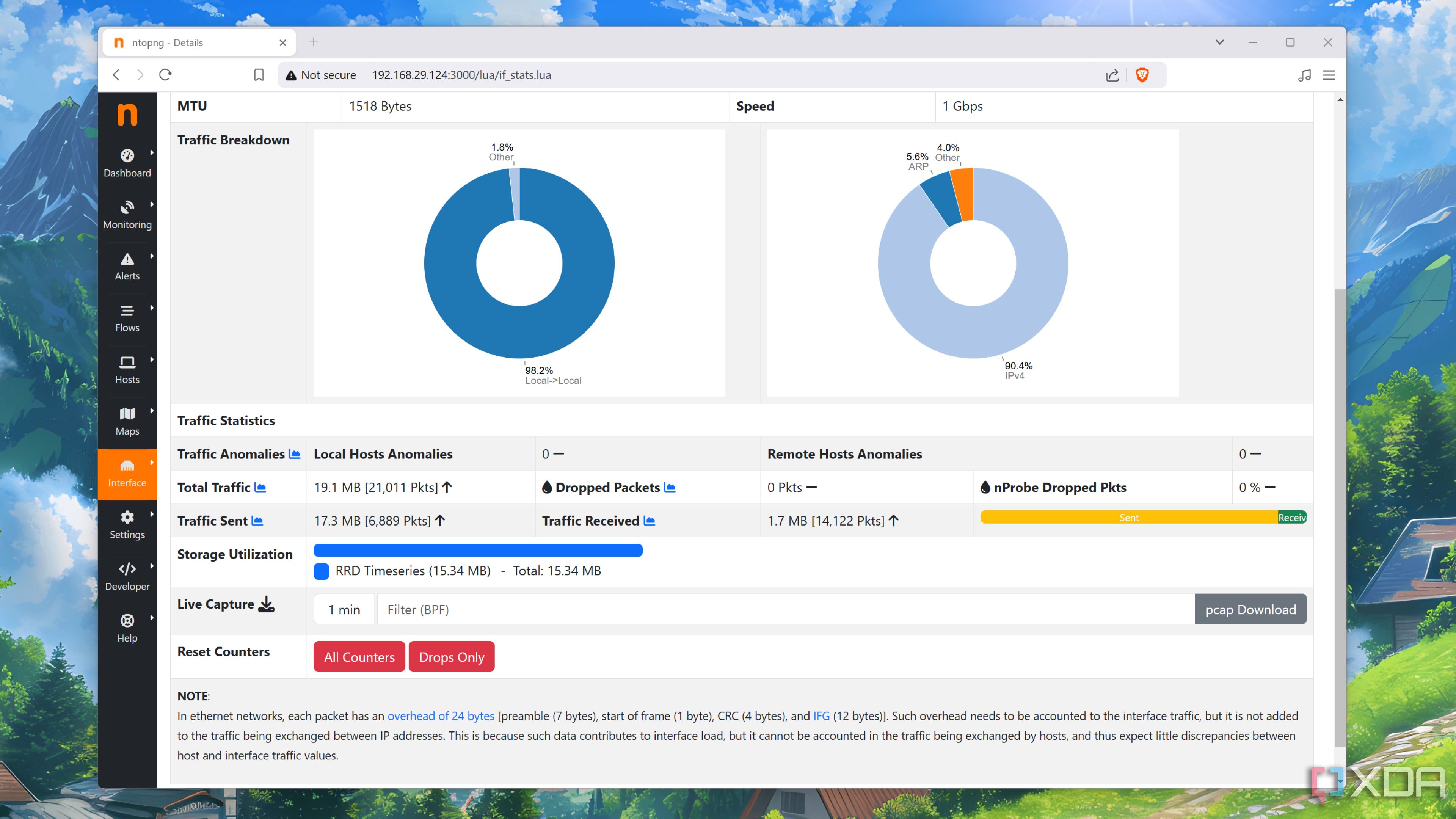
ntoping
Monitor your whole network for issues
Having deep insights into your network traffic is essential for home lab experiments. Ntopng can pull in data from traffic mirrors, SNMP devices, and more, and can analyze the traffic to identify top users, report on network behavior, and notice any unusual traffic patterns that could indicate a breach. It’s easy to set up, the free version can handle up to 8 interfaces, and you can pull in data from your wireless APs, individual switch ports, or any other network appliance you might want to monitor.
But it’s not just traffic that can be monitored. With a little setup, it can alert you if TLS certs are expiring, flag malware for your IDS/IPS system, tell you if blacklisted hosts are trying to connect to your IP address, and more. If you add Grafana and InfluxDB into the mix, you get a huge amount of data distilled into an easy-to-read dashboard to see what’s happening everywhere in your network.
Related
I monitor my home network by self-hosting ntopng – here’s how
From analyzing your traffic to snooping on malicious devices connected to your network, ntopng can do it all!
OPNsense has plenty of great plugins, these are just a few of my favorites
Once OPNsense is installed, the plugins section is the next stop. There are many options, along with these select few, and chances are you’ll be able to find a plugin for any networking services you use in other installations. It also means that your router and firewall are never static, as you can add or remove new plugins at any time to fit your changed networking needs.
#OPNsense #plugins #home #network #joy
source: https://www.xda-developers.com/opnsense-plugins-that-make-my-home-network-a-joy-to-use/