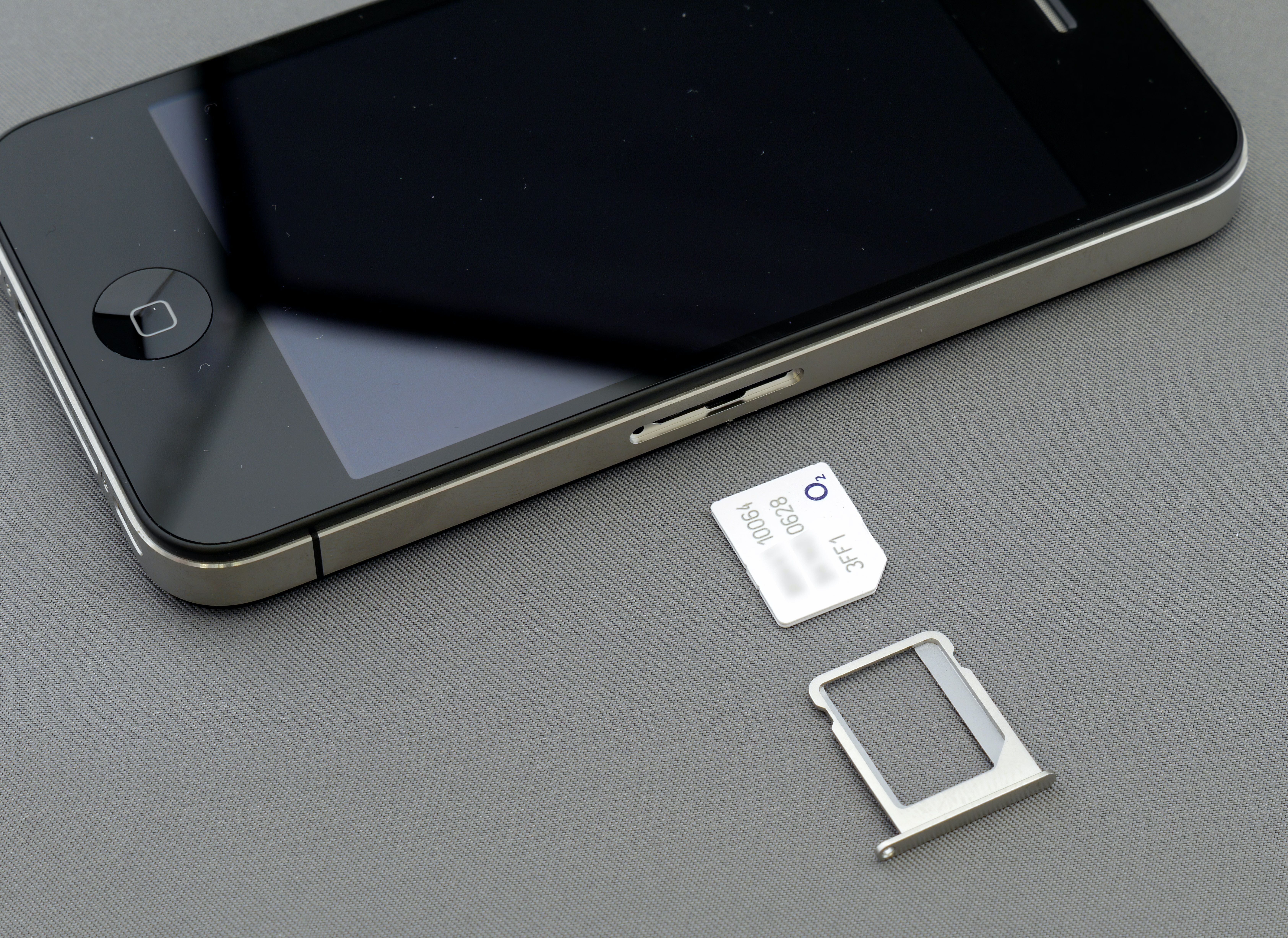
MFA, or Multi-Factor Authentication, has proliferated throughout our computing lives over the last decade. It largely began with SMS-based authentication in addition to a password, allowing users to add an extra layer of authentication by forcing users to enter a code sent to their phone upon an attempted login. The truth is, SMS-based authentication was never secure. Due to the inherent technology and the infrastructure around SIM cards, 2FA with SMS is not only inadequate; it also actively compromises your security, and here are 4 reasons why you should use a dedicated 2FA app instead.
Related
4
2FA apps are invulnerable to SIM-swapping
One of the most common attacks on SMS-based authentication
Source: Unsplash
SMS-based multifactor authentication was once the standard for providing an extra layer of security to your important online accounts. Although it is effective at deterring the most basic attacks, it has one weakness that truly can’t be overlooked. That weakness was exposed by SIM-swapping, a method of social engineering that allowed a nefarious actor to gain access to your phone number, allowing them to receive SMS authentication codes without ever needing access to your physical device.
Essentially, with the right information, someone could convince your phone provider to activate a SIM card with your phone number, compromising any multifactor authentication attached to it. The best way to mitigate this is to simply not use SMS-based authentication. 2FA apps are associated with your device, not your phone number, so they’re impervious to a SIM-swap attack.

Related
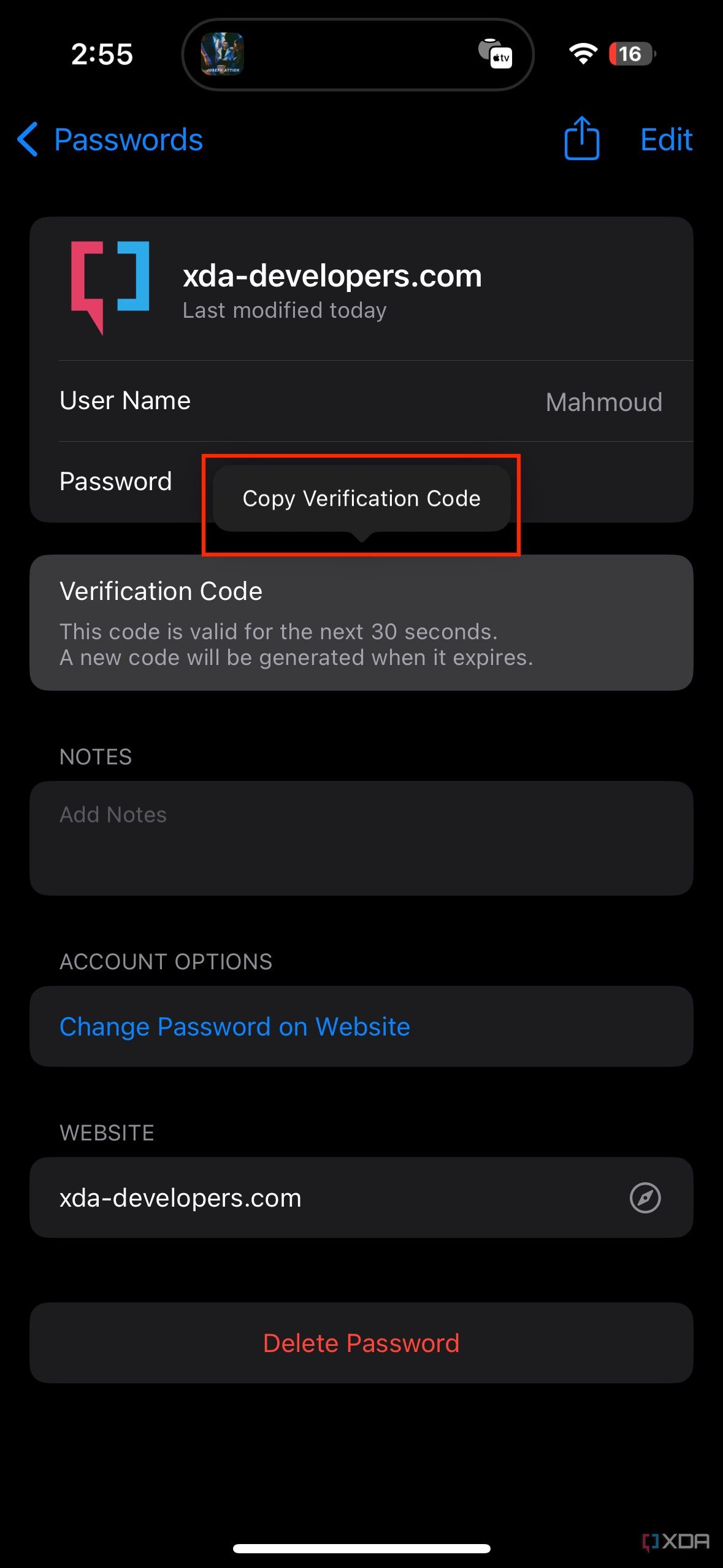
How to use the built-in 2FA code generator on iOS and iPadOS
You no longer need to rely on a third-party password manager.
3
SMS authentication can be intercepted
Where there’s transmission, there’s vulnerability
While SIM-swapping is the most glaring weakness of any MFA involving SMS, it can also be intercepted due to the weaknesses in how SMS works. SMS works by using the SS7 communication protocol, which is by no means secure. Messages that contain verification codes can be (and have been) intercepted. This can happen with nearly any kind of unencrypted information being transmitted, which awards another point to dedicated MFA apps. Generating codes on device means there’s no transmission to intercept, allowing your MFA to be rock solid instead of being a liability.

Related
Think you can hack into Apple’s private AI clouds? There’s $1,000,000 in it if you can
Crack the toughest digital vault and score a huge amount of money.
No more waiting for a message
Receiving authentication codes via SMS isn’t just insecure, it’s also just plain unreliable. It’s happened to all of us: waiting for that SMS authentication code that takes ages to arrive, or heaven forbid, one that never arrives. With a dedicated MFA app, your codes are always there, ready for you to copy and paste. Some apps even show you the next code that’s queued up, so you don’t have to feel like you’re racing against the expiration timer to get the code entered in.

Related
5 reasons you need to consider Proton Pass as your next password manager
Proton Pass is a free-to-use password manager with advanced monitoring and security features that I think you’ll love.
1
2FA apps can be used with many different devices
Access your MFA from anywhere
While SMS-based authentication is tied to your phone number, MFA apps can be associated with any number of devices, including wearables. This not only makes accessing your authentication codes a lot less of a drag if you happen to misplace your phone, but you also get the security benefits of whichever device you use, so long as the app supports it. This includes your device’s biometric security, like Face ID or Windows Hello. This ensures that even if someone were to gain access to your device, they would still be locked out of your dedicated MFA app.
Related
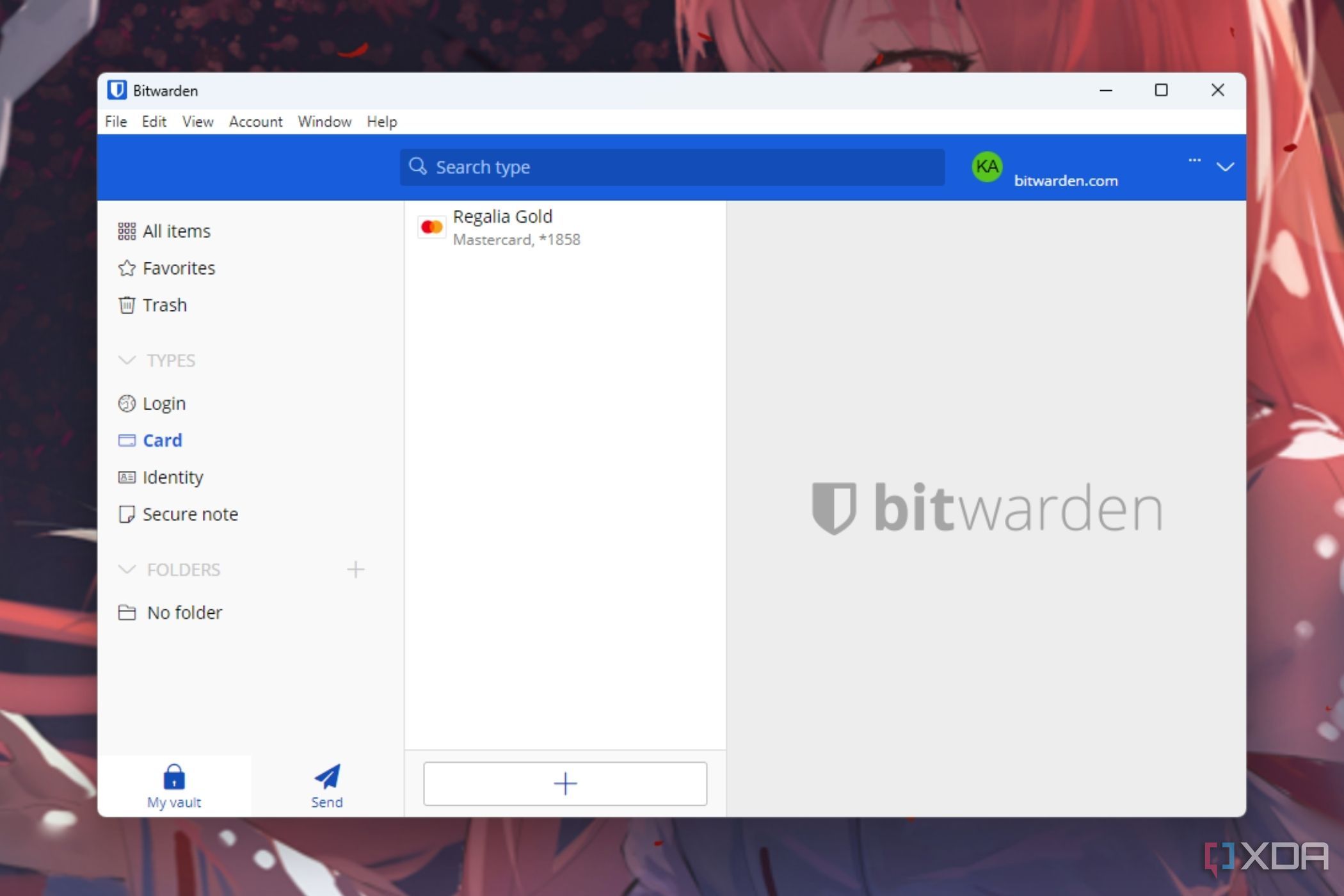
4 best alternative password managers to Bitwarden
You should consider these services if Bitwarden is out of the question.
Don’t bother with SMS 2FA any longer
There’s virtually no reason to continue using SMS-based 2FA in today’s landscape. It’s woefully insecure compared to options that are free and easy to switch to. The only downsides are due to its inherent strength; having codes produced by your physical device means that you must save backup codes in case you switch devices. Thankfully, so long as you remember to save them and store them someplace safe, you should have no problems with your dedicated MFA app.
#reasons #2FA #apps #SMSbased #authentication
source: https://www.xda-developers.com/4-reasons-you-should-you-use-2fa-apps-over-sms-based-authentication/