OPNsense is a powerful firewall forked from pfSense and based on FreeBSD. Although capable, many may find the software daunting when first starting with a custom firewall. OPNsense is pretty much good to go once installed, outside of configuring access to your Internet Service Provider (ISP). I’ve rounded up some things I always do when setting up OPNsense. Following these steps will get you up and running with a feature-rich LAN without compromising security.
8
Make sure everything is working
Run some system tests
After connecting to your ISP, it’s important to check everything is working well. Failing to do so could result in you struggling to connect to servers outside your home. It’s also vital to make sure the hardware you’ve installed OPNsense on is up to the task of handling all your network traffic. Depending on the device you’ve opted to use for your firewall — and where it’s positioned — you could run into some trouble regarding waste heat, generated by the CPU.
Running OPNsense isn’t terribly demanding, but the CPU has to handle everything on the network.
7
Update all the firmware
Being up-to-date is smart
Like anything else with firmware or an OS, it’s important to be running the latest version of OPNsense. This ensures you have all the latest features and security patches for not only the underlying OS but everything else that runs atop of it to create a powerful firewall. Thankfully, updating OPNsense takes a few minutes, and everything is automated once you click the magic button. Check once a week to make sure everything is running the latest release, and you’ll be armed and ready to handle anything.

Related
9 things to avoid when building your dream OPNsense firewall
Building your own firewall can be incredibly rewarding, but here are some things to watch out for.
6
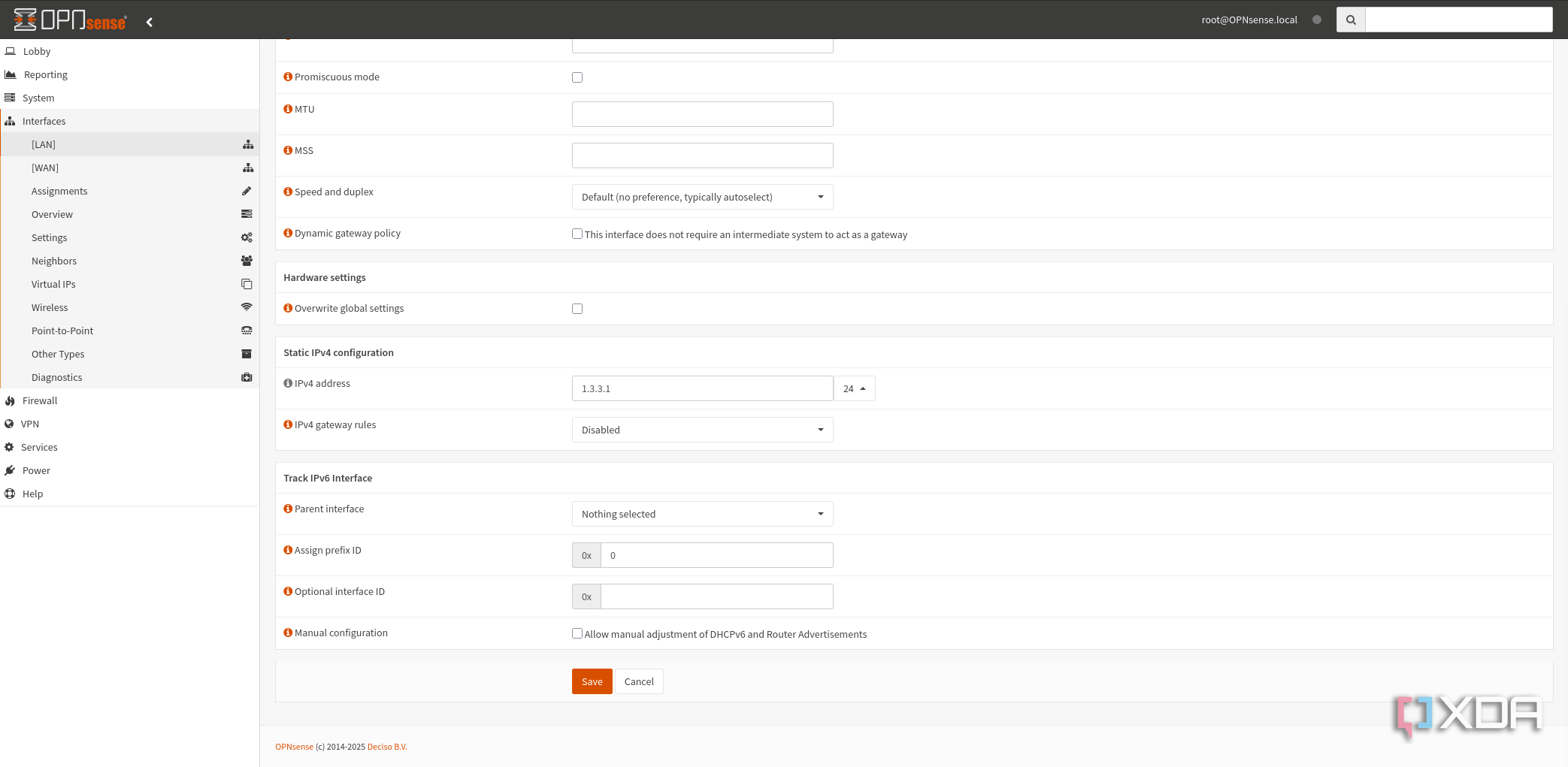
Change the LAN IP
1.3.3.7
192.168.1.1 is usually the default gateway for most ISP-supplied routers and it’s no different with OPNsense. I recommend changing the default LAN IP to something unique, which can also help with conflicts when using VPNs to access home services while away and on different networks. It can be anything you wish, so long as you remember that any static configurations would need to be adjusted and make necessary changes to copied commands when following guides.
5
Create a static IP range
For all your permanent hardware
I always recommend configuring static IP addresses on the router side rather than clients as it ensures there are no conflicts between hardware with the same settings. OPNsense’s DHCP server can achieve precisely this, allowing you to set a static IP reserved for each device. I would carve out a range of IP addresses for static IPs to make it easier when using them. You can reserve a block, for example, 1.1.1.10 to 1.1.1.30, where the DHCP server will ignore any within this range.
This can be handy when setting static IPs for all your network hardware, services, and other devices. You can then group these IPs within the range, so all your switches and APs could use 1.1.1.10 to 1.1.1.15 and all your Docker containers could use 1.1.1.16 to 1.1.1.25. DHCP can then use the rest of the available IPs for assigning addresses to new clients.

Related
6 best practices for deploying pfSense or OPNsense in your home lab
Home lab life is all about learning, and already-established best practices will help your journey.
4
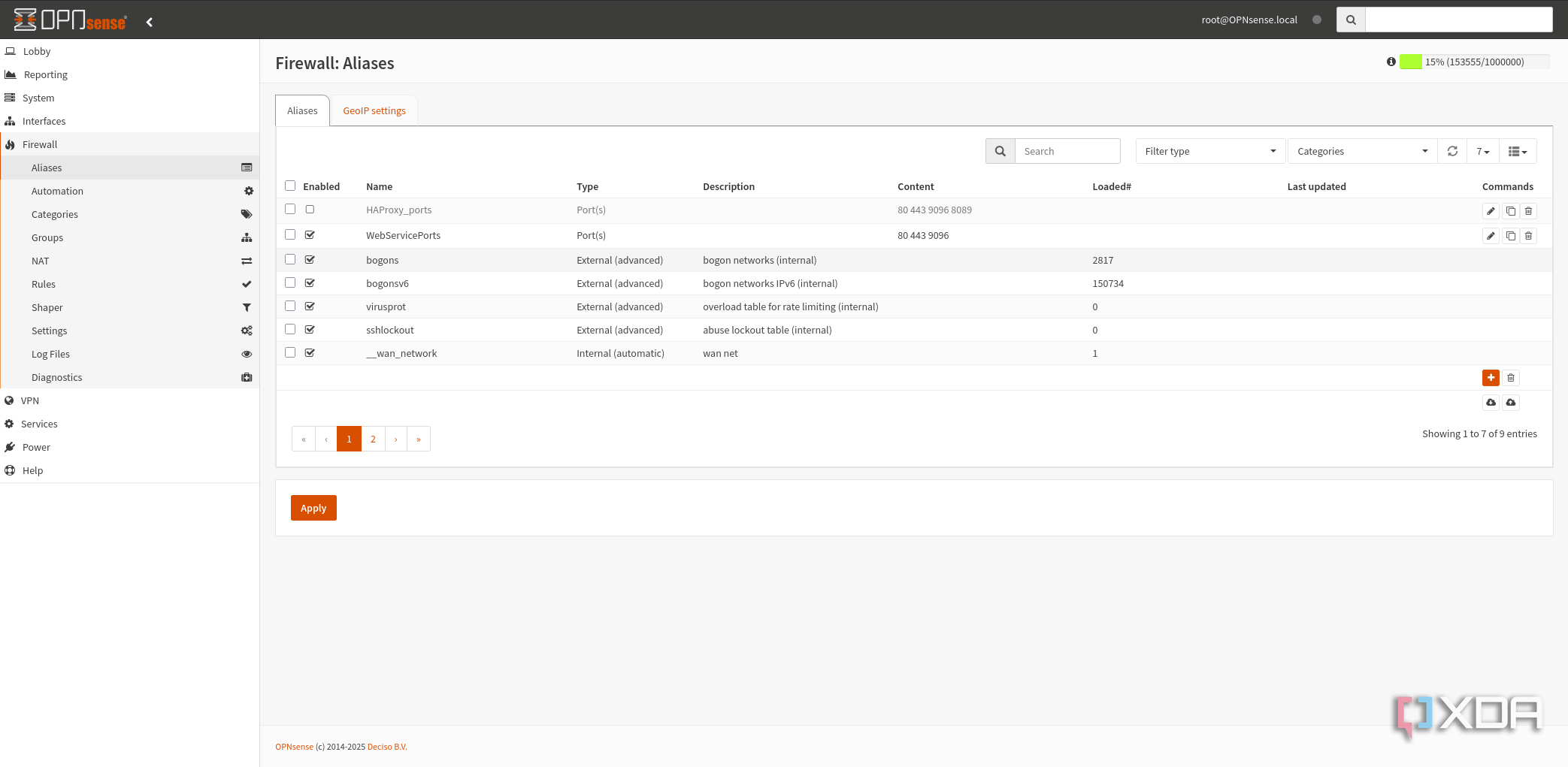
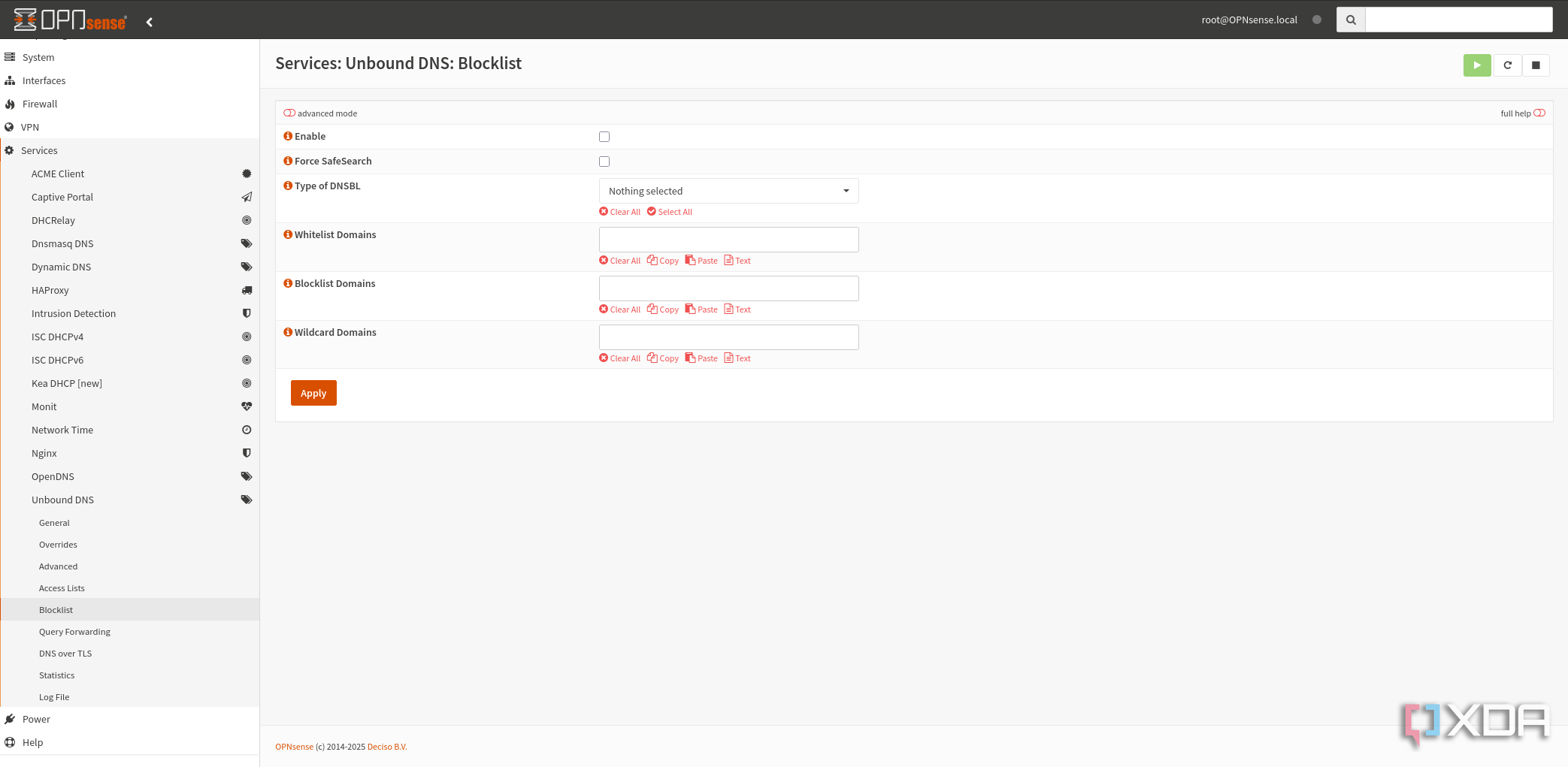
Blacklist dodgy domains
Protect your entire network
Using Unbound, you can block malicious domains reported by the wider community. OSID is a compilation of domains known for advertisements, phishing, malvertising, malware, spyware, ransomware, cryptojacking, and unnecessary telemetry or tracking. It’s an important tool in the arsenal of a LAN admin to protect their network and everything connected to it from harm. It takes a few minutes to configure through Unbound, and you’re good to go.
3
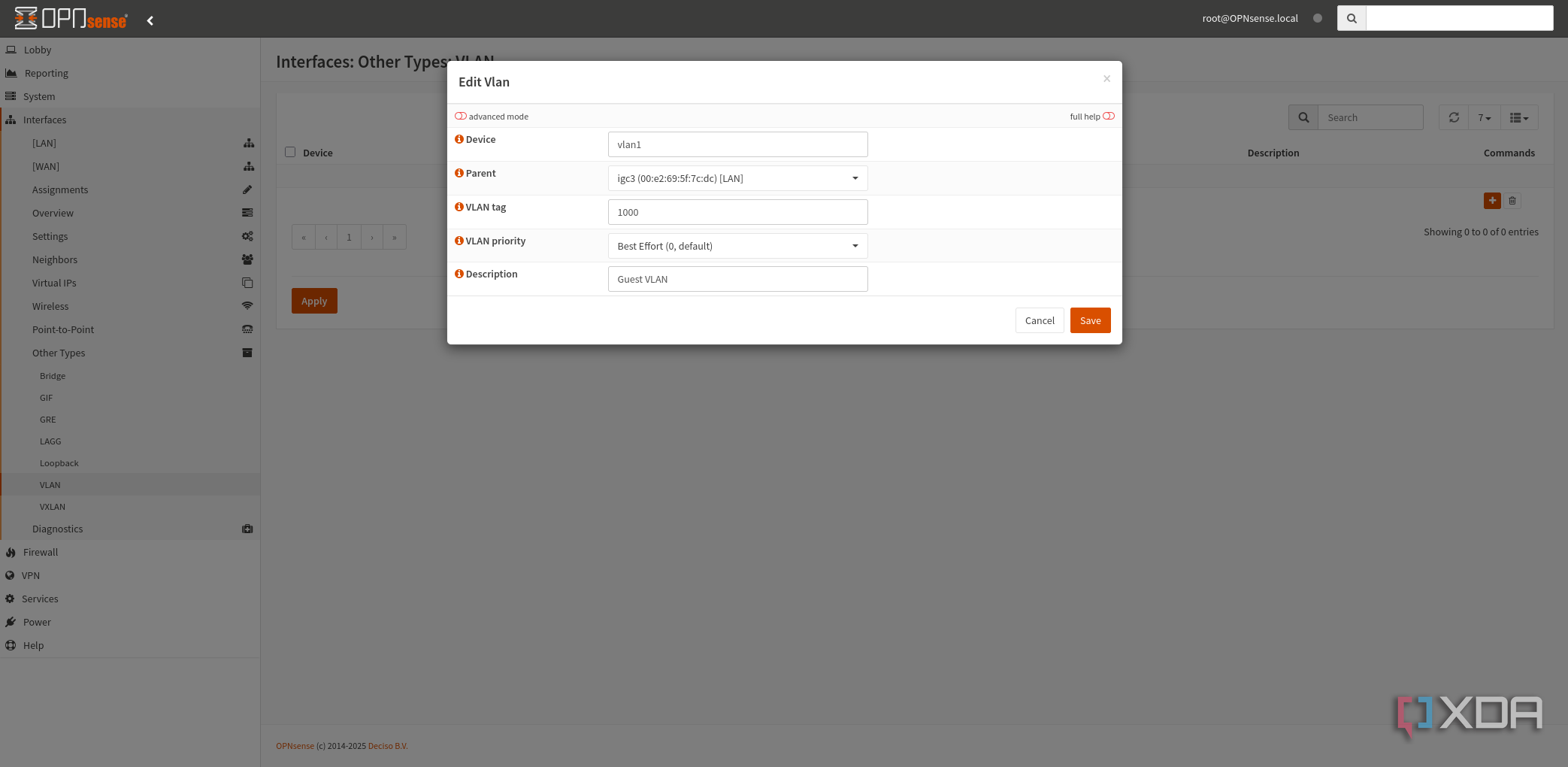
Create virtual LANs
Guest network for visitors
VLANs are a powerful tool for partitioning your network into segments. Instead of investing in additional physical hardware to create multiple networks, you can virtualize one using existing infrastructure. That means your firewall, switches, and access points can all handle multiple networks. This can prove useful for creating a separate network for guests, which can use an SSID that doesn’t interfere with local traffic. The same goes for IoT hardware or anything else you wish to keep separate.

Related
3 reasons you should you be using VLANs on your home network
Virtual LANs are excellent for creating the perfect network.
2
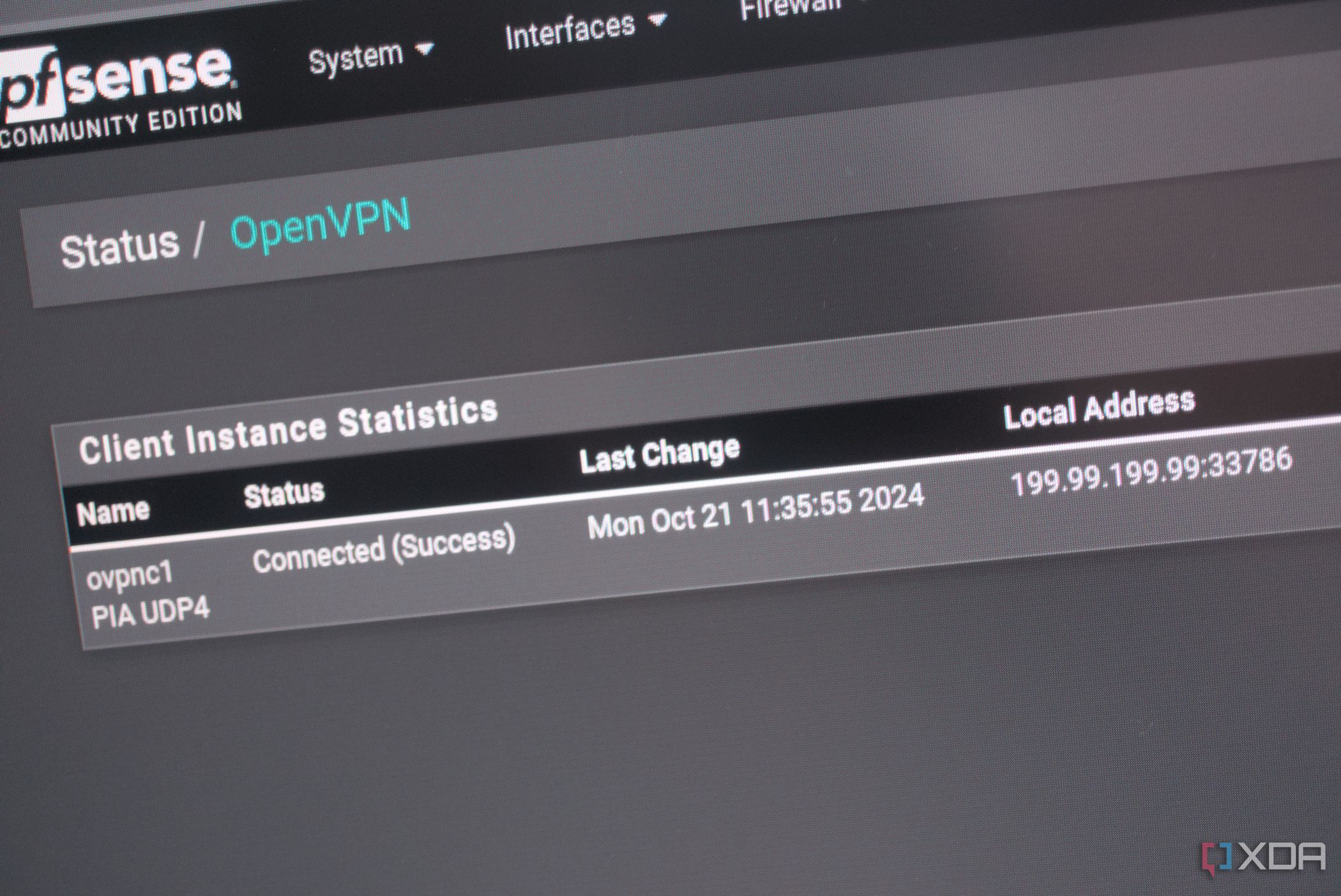
Set up a LAN-wide VPN
Using your favorite provider
Protecting yourself with a Virtual Private Network is a great way to stop anyone from snooping on your connection. It’s also handy for accessing restricted content or for getting around blocks. Setting up a VPN on multiple devices can take some effort, especially if it involves products owned by those less tech-savvy. That’s where a network-wide VPN comes into play. You can use OPNsense to connect to your VPN provider and create blanket coverage for all devices on the network.
The best part about segmenting your network is grouping some IPs that can be excluded from the VPN, allowing you to get around issues relating to using such a service. This can be handy for gaming and issues relating to websites not working properly.
Related
How to stop everyone snooping on you with a VPN and pfSense
Get your very own VPN up and running across your entire home network.
1
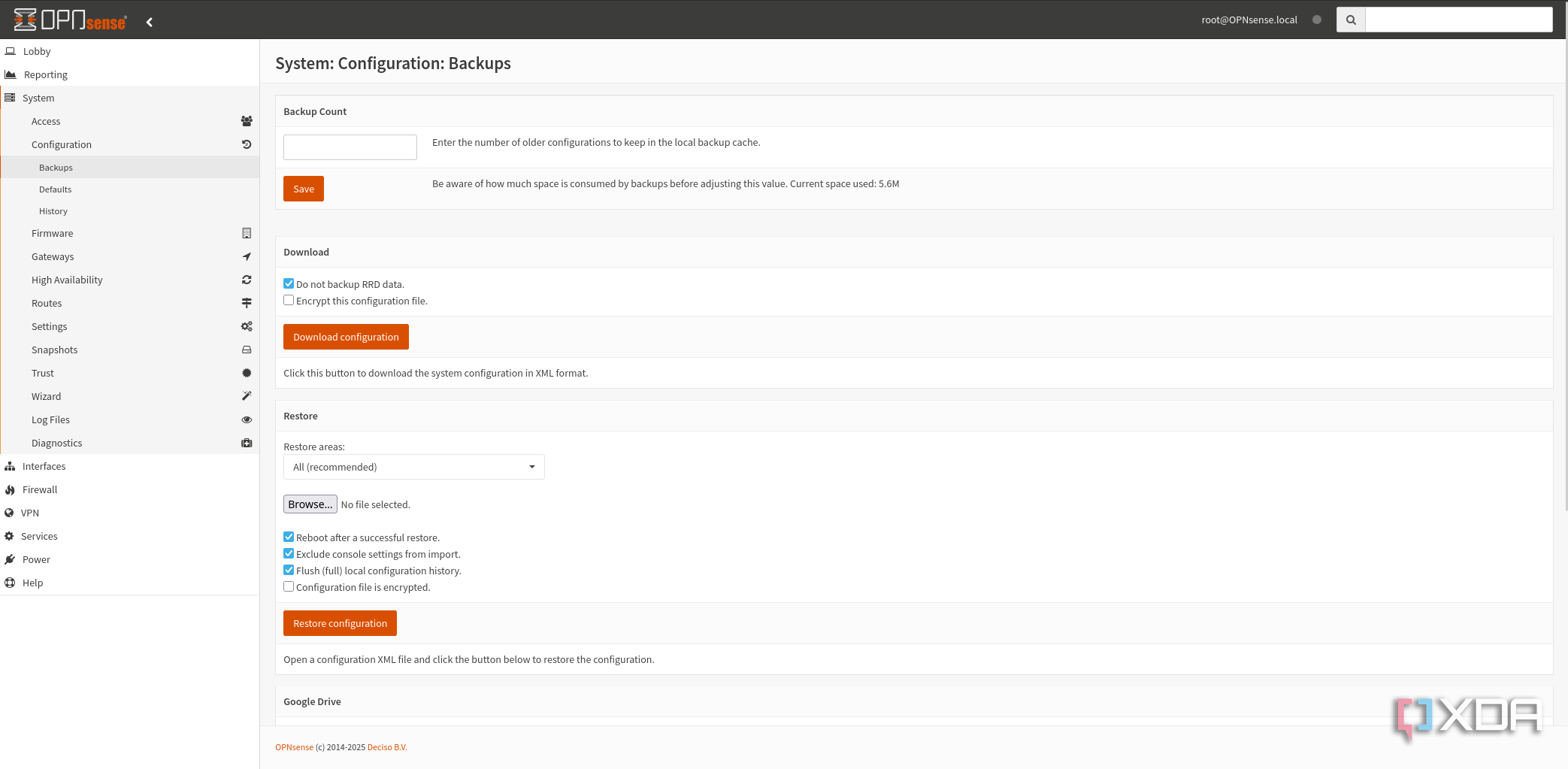
Back up the config files
Just in case something goes wrong
You’ve spent all that time and effort to configure your dream firewall and everything is working flawlessly. It’s time to back everything up! Something could go wrong where you’d need to reinstall OPNsense and using a backed-up configuration file can restore the firewall to how it was when you finished toying around with the web GUI. Like learning anything new, we’ve all been there where something is mistakenly configured that breaks everything, and OPNsense is no different.
It can also prove useful to take backups when toying around with OPNsense so you can quickly return to how the firewall was configured before the latest changes were applied.
Learning how your LAN works
A great part about using a custom firmware such as OPNsense is the ability to learn new things. You’ll be in control of everything on your network, including support. Should an issue arise with your LAN, you’ll be the first (and last) port of call, which will consist of some troubleshooting and research. Every time you interact with OPNsense and everything on the LAN, you’ll learn something new. An ISP router can prove useful and does support many of the features OPNsense offers, but you’ll likely miss out on something.
ISP hardware is also completely closed. You can’t do anything to the device or the software installed — You’re also at the behest of your ISP for them to continue supporting this router. Then there’s the fact that it’s from your ISP and likely isn’t designed with your privacy in mind. OPNsense is first and foremost a firewall that works for you. With a VPN configured for network-wide protection, you’ll be mitigating any possibility for your ISP to snoop in on your connection.
#installing #OPNsense
source: https://www.xda-developers.com/things-i-always-do-after-installing-opnsense/