Home labs are perfect for honing your skills while not destroying your home network in the process. But while you’re building out your home lab’s network capabilities, how do you actually ensure that the two stay separate? A dedicated firewall is what you need, whether a dedicated hardware device or a virtual one. With the right rules in place, you can keep your home network safe from your home lab experiments and still have access to the internet at large.
Related
9 reasons I’m going with a prebuilt hardware firewall instead of making my own
The home labber in me is recoiling in horror but I’ve found a hardware firewall that just works, and I’m not going back.
5
Turn off UPnP
You want to be in full control of your home lab
UPnP was created to fix IPv4 address shortages, which makes sense if you’re opening all your devices to the internet and don’t know how to configure things manually. However, this is a home lab. You’ll be manually configuring your IP ranges and several VLANs, and the only things you want going through your firewall rules are those that you personally allow.
You don’t need or want UPnP enabled. It will mock your other carefully crafted firewall rules designed to safeguard your self-hosted apps and services. Plus, you don’t want random devices opening their own ports to the outside world.
The only time you might want UPnP on is if your home lab is designed to study the behaviors of untrusted devices. In that case, you’ll likely have those in their own VLAN with plenty of packet monitoring to find out where they might be dialing back home.

Related
4 reasons you should consider disabling UPnP in your router
You probably don’t need it anymore, and it’s a security nightmare.
4
Set a rule to drop traffic by default
You want all traffic coming through your home lab firewall to be approved
While application-specific or device-specific allow rules are important, there’s one rule that’s the most important for your home lab firewall. That’s a catch-all deny rule that’s the last rule at the bottom of the hierarchy, to deny any traffic that isn’t implicitly allowed by a pre-existing rule. You want this because any service that’s opening ports to the internet that you’re not allowing with a dedicated rule is a security issue, and we all want to use best practices in the home lab.
That means you’ll end up with a hierarchy of firewall rules that looks similar to:
- Anti-spoofing rules: The top level of rules filter all traffic, but only let through packets from legitimate sources.
- User access rules: Now you set up rules for what users can do, like HTTP for web access, 443 for VPNs and similar.
- Management access rules: Rules for allowing admin tools and addresses come next, so only trusted sources can interact with the configuration and monitoring of the firewall.
- Service-specific denial rules: Blocking unnecessary or vulnerable services, and Geo-blocks, reducing noise and attack vectors.
- Catch-all deny rule: Drops all traffic that doesn’t match any of the previous rules that explicitly allow it through the firewall.
This rule is deceptively simple, but it’s the most important one to get right and to place in the right place in the structure so that it is not overruled by any other rules.
Related
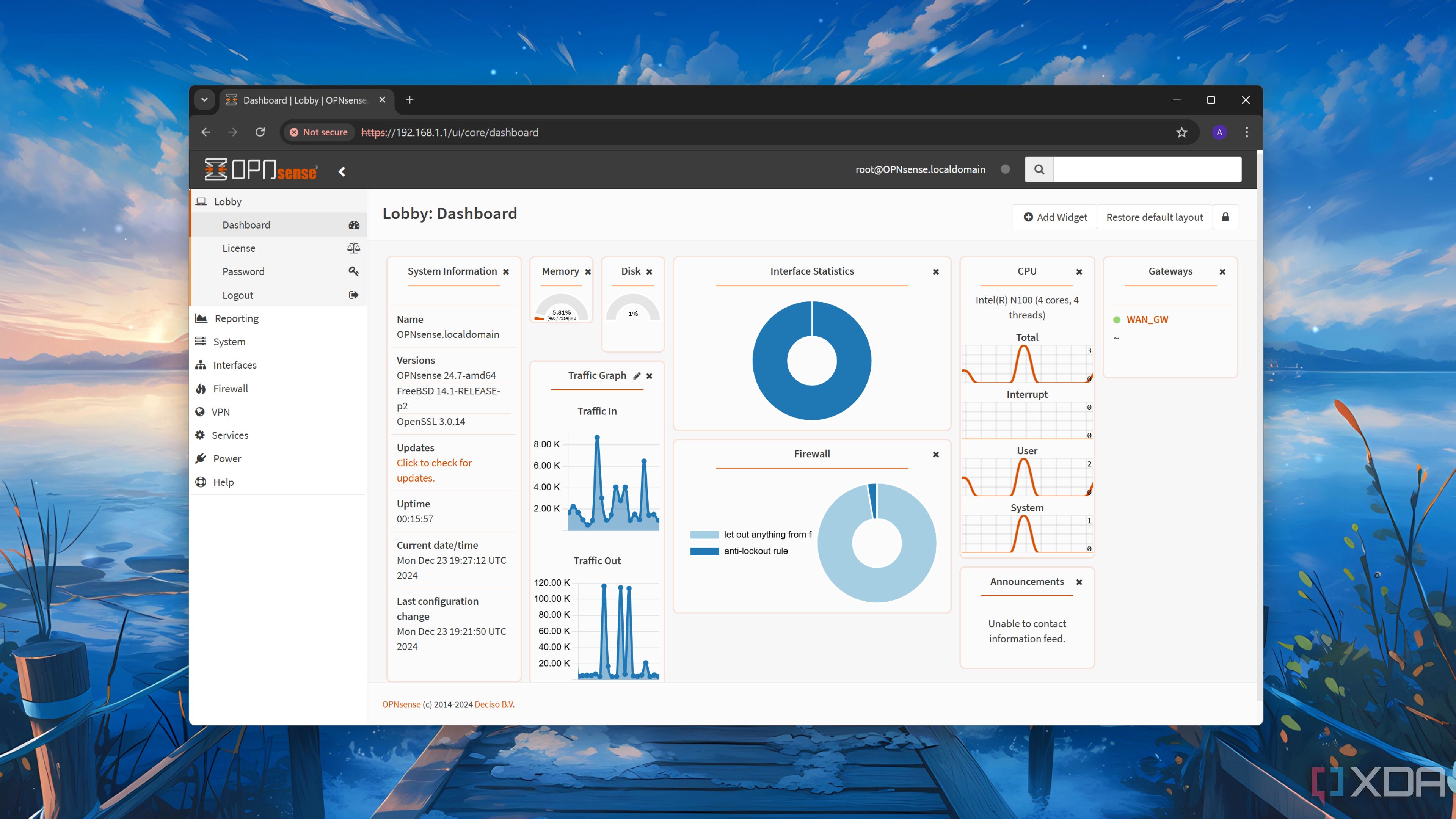
How did OPNsense fork from pfSense and become a better firewall?
OPNsense and pfSense have the same origins, but OPNsense is now the go-to recommended firewall.
3
Segregate things with VLANs
This is especially important for the management layer and any smart home devices
You should probably be using VLANs on your home network as well, but if you haven’t dipped your toes in yet, the home lab is the best place to start. For starters, there should be one VLAN dedicated to the management layer of your home lab equipment, and the IP range for this VLAN should never be tampered with. You’re going to be doing a lot of experimentation, and that means you will likely get locked out of network equipment, but having a dedicated management VLAN means you can always get back in to fix your access.
Then there should be VLANs to group servers together, one to keep any IoT and Home Assistant devices away from your data-containing devices, and any other VLANs you might think are handy to have. Don’t forget a DMZ VLAN as well, so you can stick untrusted devices in there for testing until you decide they’re benign enough to add to the trusted sections.

Related
6 things you need to know before setting up VLANs on your home network
VLANs are super handy for organizing your network, but you need to do some prep work first
2
Set everything to use a Pi-hole for DNS queries
You can run a dedicated SBC or virtualize this if it’s easier
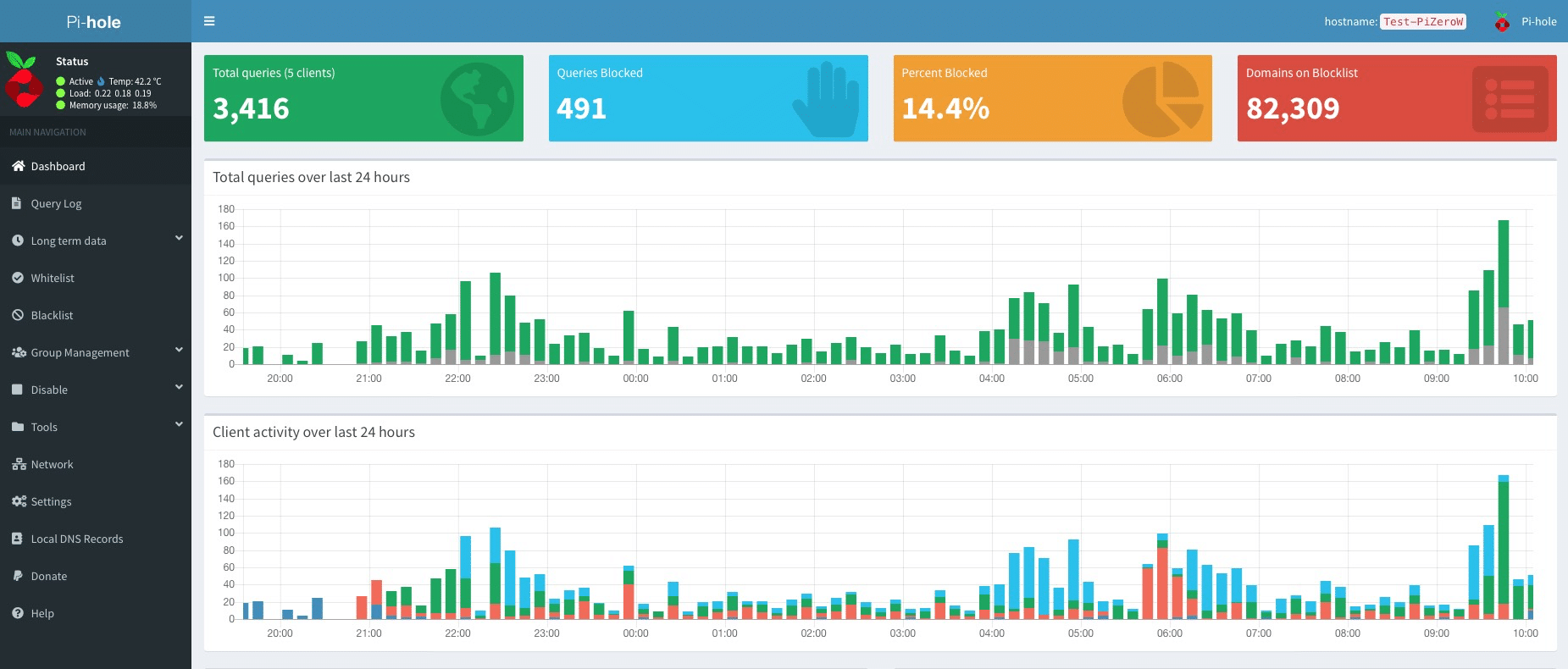
Source: Pi-hole
Even if you trust every device in your home lab, you should always operate on the principle of least access. DNS queries are absolutely necessary for your home lab devices to have access to, but you don’t want them to have unsupervised access, either. By pointing devices to DNS running on a Pi-hole, you can visualize all DNS requests while also keeping your home lab secure and protected from advertising, malicious domains, and other unwanted annoyances.

Related
6 Raspberry Pi projects for smarter home networking
For smarter home networking, look no further than these 6 Raspberry Pi projects.
1
Turn on IGMP snooping
Limit multicast traffic to those devices that request it
IGMP, or Internet Group Management Protocol, limits IPv4 multicast traffic from overwhelming the local network or VLANs. At least, it does if you have IGMP snooping enabled. Your firewall will look for multicast traffic and forward it only to the devices that are interested in receiving it.
That’s important on any network, where you can easily DDoS devices with multicast traffic, leading to annoying troubleshooting steps. If you have network monitoring set up, troubleshooting might be a valuable learning moment, but why subject yourself to the pain when you can change a firewall setting and not have to worry about multicast packets flooding your home lab?

Related
5 networking tools to safeguard your home lab from the inside out
Whether you’re a pro or new to home labs, securing your self-hosted systems is vital. These 5 networking tools will keep threats at bay.
Your home lab should be limited in how it can interact with the internet and your home network
Keeping your home lab separate from the rest of your home network is important. It educates you about network segmentation and prevents mishaps in your experiments from causing mayhem with your normal internet traffic. This is not to mention the impact it would have on your partners, kids, and roommates. With the right combination of firewall rules, you can have a strong and resilient home lab network that doesn’t impact your other internet use.
It’s also important to review the logs on your home lab periodically, and revise any firewall rules that are causing issues in services being incorrectly dropped, allowed, or any other mismatch to how you want your home lab firewall to behave.
#advanced #firewall #rules #lock #home #lab
source: https://www.xda-developers.com/advanced-firewall-rules-to-lock-down-your-home-lab/