With cyber threats evolving constantly, a robust encryption solution can provide that extra security layer you need to protect your data. Since I discovered VeraCrypt, it has emerged as a file guardian for my files. It marries top-notch encryption capabilities with user-friendly features, and that should be a winning recipe for any user. So, here’s why, for me, VeraCrypt stands out as the ultimate tool for file encryption.
Related
7 reasons you should (or shouldn’t) encrypt your NAS data
Enhanced data safety often comes at the cost of convenience
Powerful encryption and multi-layered security
Hidden volumes and multi-layered encryption
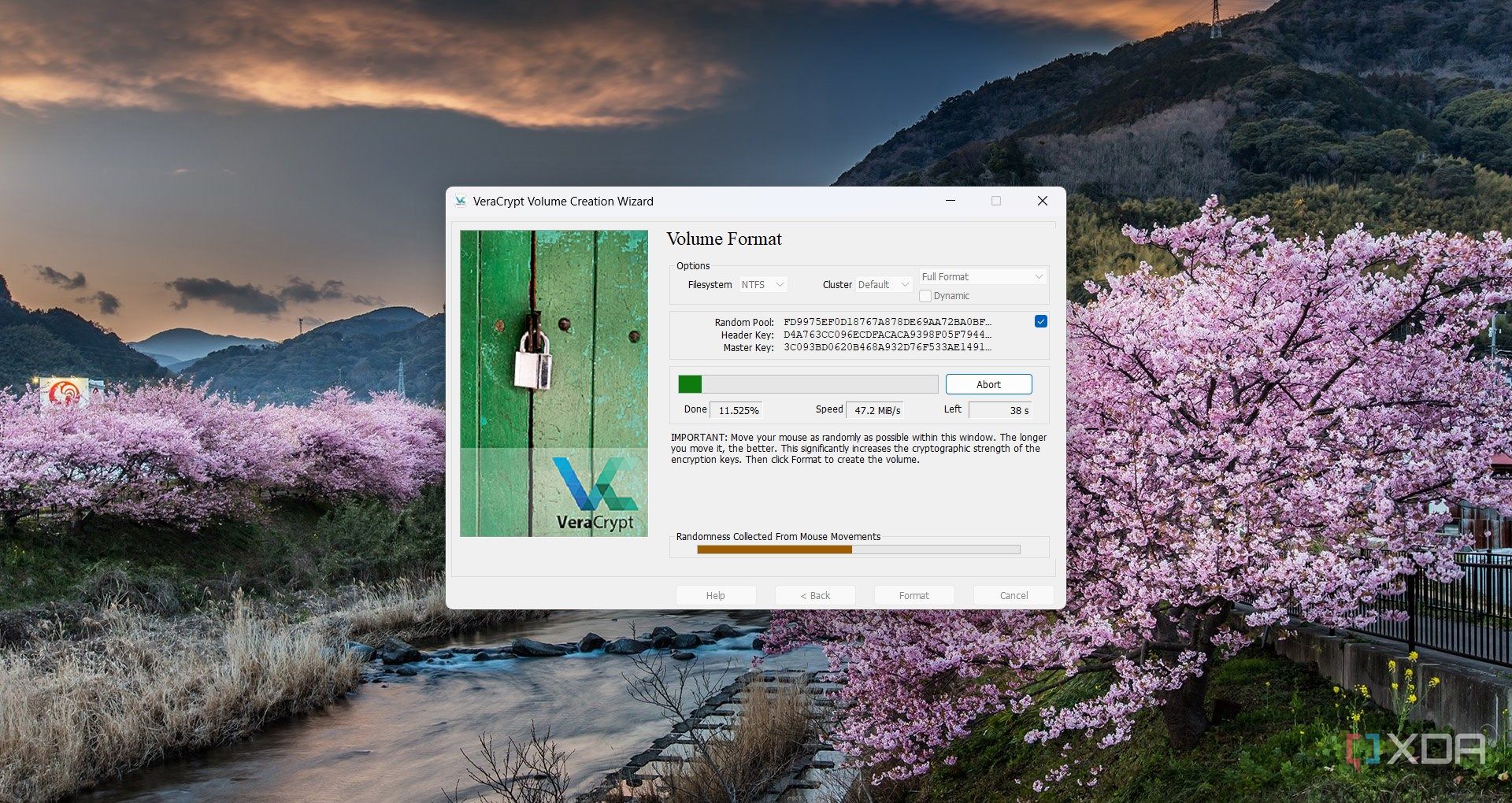
At its core, VeraCrypt leverages a range of industry-leading encryption algorithms, including AES, Serpent, and Twofish. You have the option to cascade these ciphers, layering multiple algorithms to establish a nearly impenetrable defense. The multi-layered approach ensures that even if an attacker compromises one encryption method, additional layers continue to protect your data.
The tool also uses strong key derivation functions, designed to fend off brute-force and dictionary attacks effectively. However, for me, the most practical feature of VeraCrypt is the ability to create hidden volumes. In short, you can set up decoy containers while keeping a secure, concealed volume hidden from prying eyes. So, whether you encrypt a folder with sensitive documents or an entire system partition, this tool will ensure that your data remains confidential.
Versatile encryption options for every need
It can go as far as you want
One of VeraCrypt’s most admirable traits is its remarkable versatility. It caters to a vast spectrum of encryption needs, whether you’re looking to secure a handful of files or an entire disk partition. VeraCrypt provides multiple modes of operation, including the ability to create encrypted containers and virtual disks that behave like regular drives. This feature makes it incredibly easy to transport and safeguard sensitive data on removable media or cloud storage.
If you want to protect your entire system, VeraCrypt offers full disk and system partition encryption. This ensures that even before your operating system boots up, your data remains shielded from unauthorized access. Another aspect is that you can use a cascade of AES-Serpent-Twofish encryption if you have a more powerful device, or just stick to AES-256, which is strong enough in itself.
Open-source transparency and auditable security
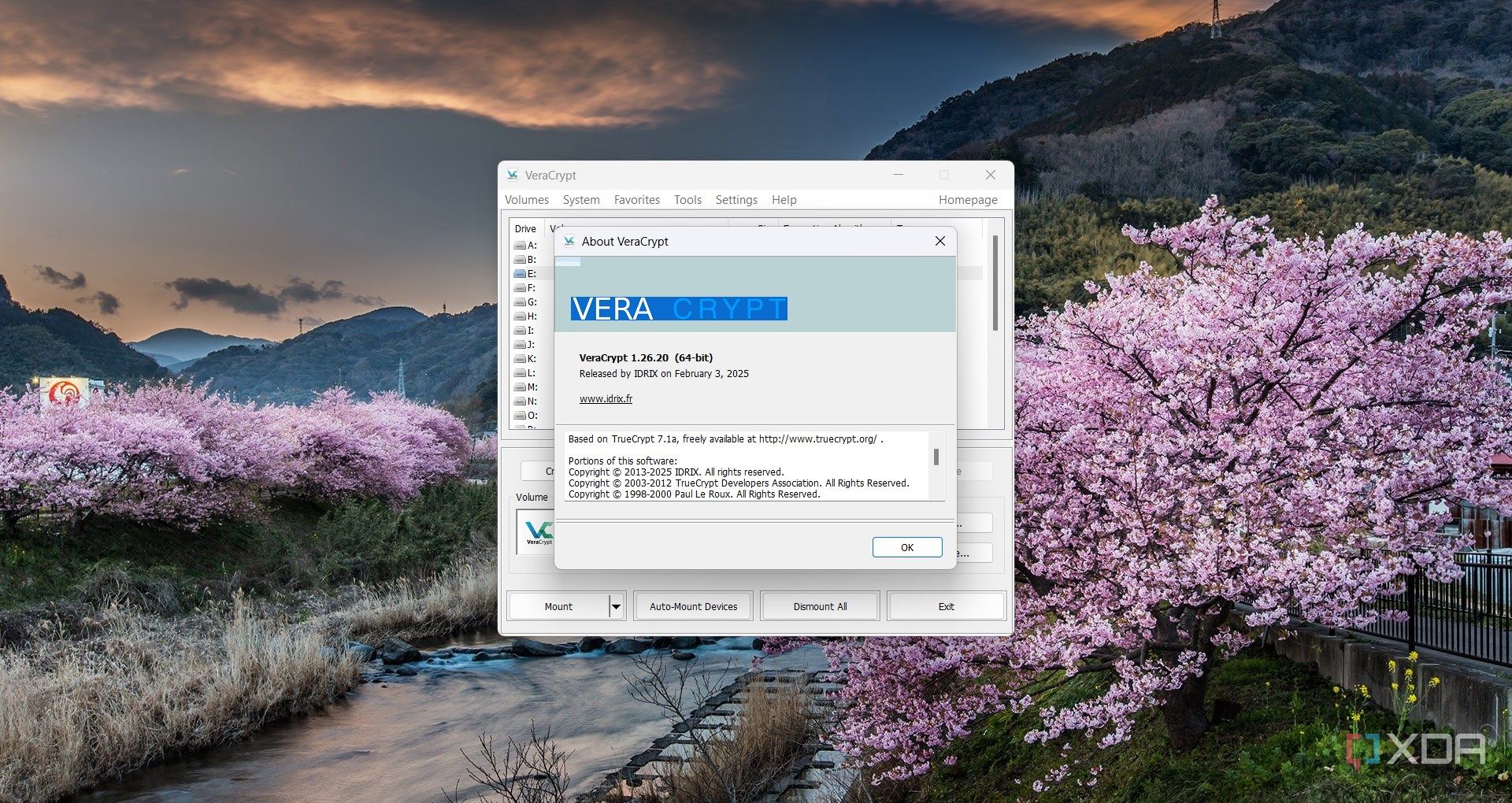
VeraCrypt is an open-source tool, and you might think it’s less powerful or reliable than paid software, but this is not the case. In fact, being open source means that its source code is freely available for review, allowing security experts and enthusiasts from around the globe to audit, test, and enhance the software. This level of transparency also guarantees that there are no hidden backdoors or undisclosed vulnerabilities, which are often discovered in some other, more reputable software.
Therefore, VeraCrypt’s power resides in the vast active community around it. The collective intelligence often reacts a lot faster against emerging threats than a corporate development department.
The learning curve is not that steep
No tool is without its minor drawbacks, and for this encryption tool, the primary challenge I’ve encountered is a not-so-steep initial learning curve. Initially, configuring advanced features like hidden volumes or fine-tuning encryption parameters required a bit more time and patience than I had anticipated.
For someone new to encryption, the array of options and the technical terminology can be somewhat daunting, leading to a period of trial and error. This initial complexity might frustrate users who are seeking a plug-and-play experience.
However, this counterargument is easily overshadowed by the long-term benefits. Once the basics are mastered, with the help of comprehensive documentation and community tutorials, you will soon achieve the desired results.

Related
4 reasons your cloud provider should be using end-to-end encryption
Using zero knowledge architecture and E2EE makes the web safer for everyone.
The user-friendly experience helps a lot
The UI is not that intimidating after all
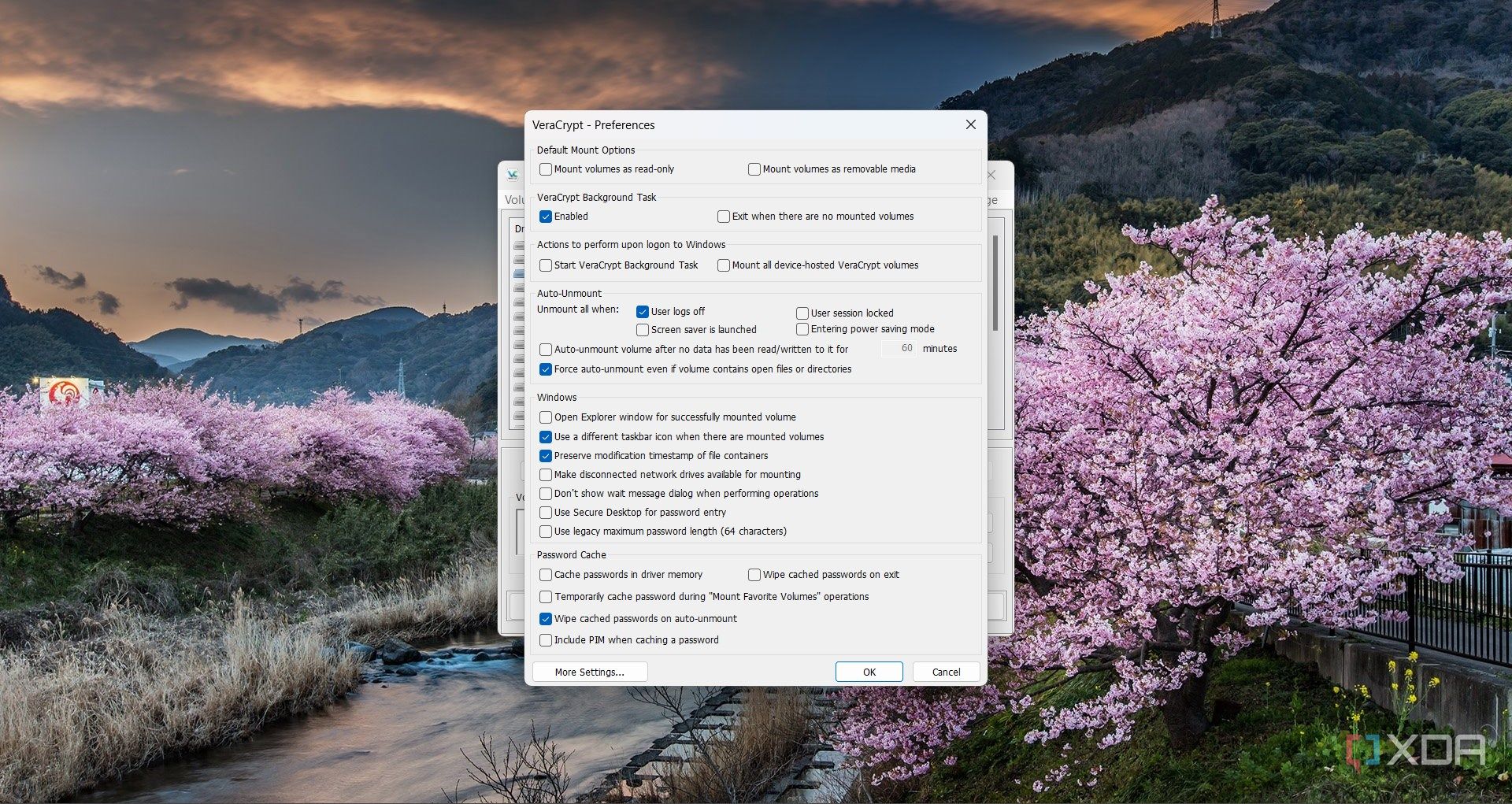
Although, as I’ve mentioned above, VeraCrypt is not really easy to comprehend at first, it does have a pretty simple and friendly interface. After the initial setup, it becomes accessible to both beginners and experienced professionals.
Whether you’re setting up a simple encrypted container or configuring an entire system drive, you have step-by-step instructions and clear labels to help you in the process. That eliminates much of the common intimidation you might experience at first.
At the same time, you’re not shortchanged if you’re an advanced user. VeraCrypt offers a comprehensive range of customization options, from selecting specific encryption algorithms to setting up hidden volumes and partition-level security configurations.

Here’s why I’m sticking with VeraCrypt
To be completely honest, I will probably never use all the features that VeraCrypt has to offer. My usage is limited to encrypting some sensitive data folders using AES. I’m just a home user looking for an extra security layer, not a government agency.
However, if you do need system-wide encryption, VeraCrypt will also deliver on that purpose. This flexibility makes it ideal for both simple users and organizations. However, the only downside is that using it within an organization also comes with some accountability guarantees that open-source software can’t deliver.
#VeraCrypt #choice #encryption #software #Windows #I039m #sticking
source: https://www.xda-developers.com/started-using-tool-encrypt-files/