Key Takeaways
- Set complex passwords and enable 2FA to enable secure logins on your Proxmox server.
- Create VLANs for virtualized guests to isolate insecure containers.
- Limit port access and set up router/firewall VMs for additional security on your Proxmox.
As one of the most popular platforms for home labs, Proxmox packs all the features you’ll need for your virtualization projects. But just like every other computing device, the Proxmox host machine – alongside the VMs and containers running on your server – can still get infected by viruses, ransomeware, and other types of malware hellbent on ruining your day. Thankfully, there are a couple of ways to reduce the vulnerabilities in your home lab environment. So, we’ve compiled a list of the best precautionary actions you can take to safeguard your Proxmox server.
7 Set complex passwords
And enable 2FA for your users
While it may sound rather obvious, changing your password to Eldritch-sounding chants is one of the most foolproof ways to safeguard your Proxmox machine from intruders attempting to log into the system. To add an additional layer of security, you can enable Two-Factor Authentication using the Proxmox OATH facility.
You can do so by heading to the 2FA tab inside the Permission section of the Datacenter and selecting TOTP. Once inside, you can open the QR code inside an authenticator app and enter the token under the Verify Code section. Proxmox will ask you for the 2FA token the next time you log in with the specified Username.
6 Create VLANs for virtualized guests
Ideally, you’ll want a managed switch to make full use of VLANs
If your Proxmox workloads involve connecting IoT gadgets and other vulnerable devices to your home network, you’ll want to run them inside VLANs. For the uninitiated, VLANs allow you to split a physical connection into multiple virtual connections, where you can isolate different groups of devices.
To enable VLANs on your Proxmox host, navigate to the Network tab of your Proxmox node and turn on the VLAN aware feature for your network bridge. After that, you’ll need to open the nano /etc/network/interfaces script through the shell and insert the VLAN IDs before using them to create a new VLAN bridge for your Proxmox containers. Although there are some workarounds that you can use to run Virtual LANs on cheaper unmanaged switches, I recommend grabbing a managed switch to make full use of this facility.
5 Limit port access as much as you can
Make sure you don’t accidentally disable the essential ones!
Open ports are one of the biggest security vulnerabilities for any computing setup – and Proxmox is no exception. Sure, you’ll want to keep certain ports like 443 (HTTPS) and 3128 (SPICE proxy) accessible to avoid running into issues when using the services associated with them. But depending on your use cases, it’s a good idea to edit the firewall rules to deny traffic on certain ports.
You can do so by heading to the Security rules tab under the Firewall section of the Datacenter and adding a new Group with custom Rules for the ports. Pair that with VLANs, and you’ve got a robust security system for your VMs. But you can take this setup to a different level with another level by turning your Proxmox hub into a router…
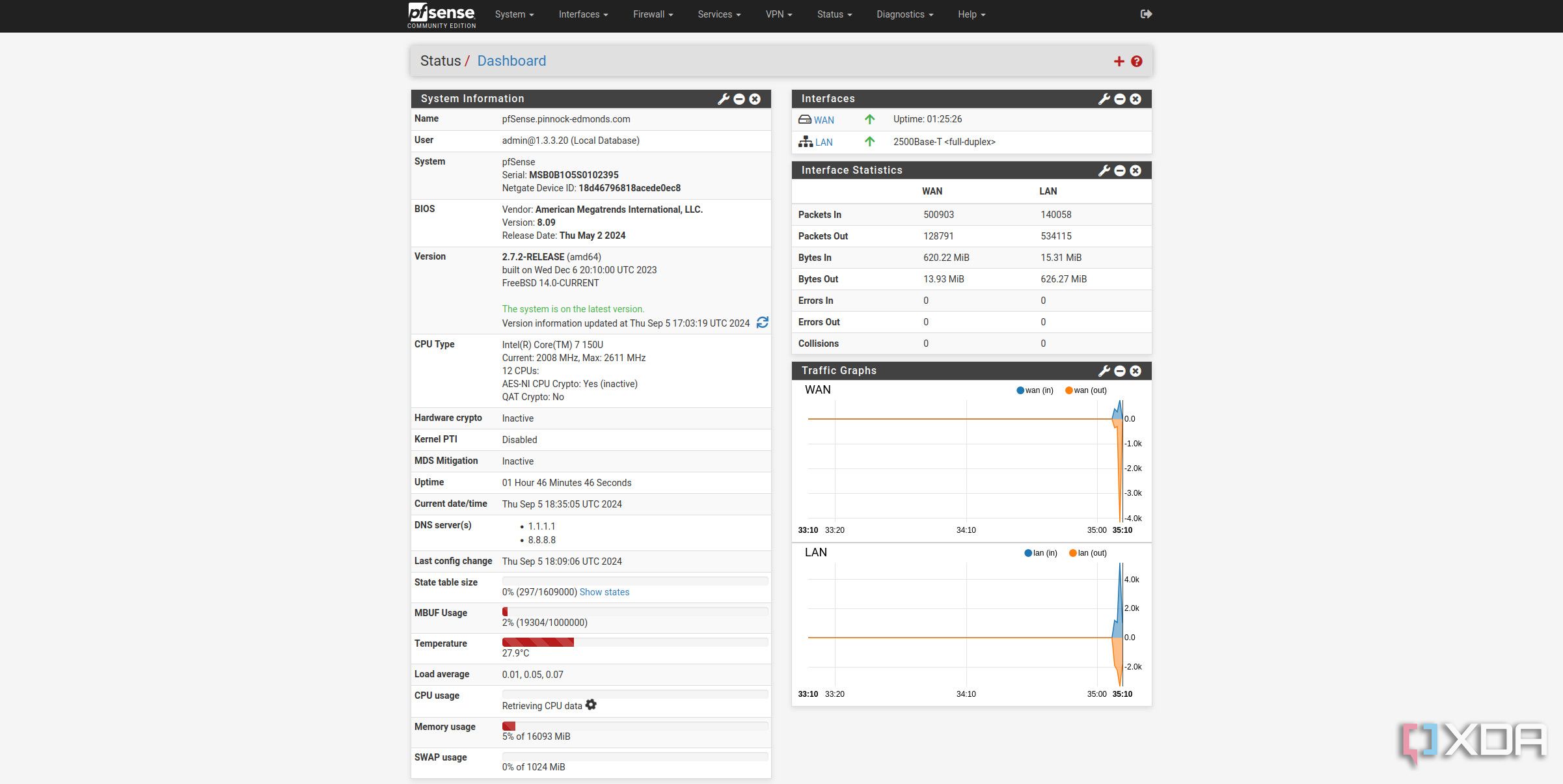
4 Set up router/firewall VMs
OPNsense or pfSense: Pick your poison!
For the maximum security, you might want to run a dedicated firewall utility inside a Proxmox VM. Whereas the Proxmox firewall will only protect your virtualization server, running a full-fledged router OS inside a virtual machine can help you set firewall rules for all the devices on your network.
Depending on which faction you owe your allegiance to, you can even choose between pfSense and OPNsense as the OS for the VM. Despite all the benefits of a Proxmox-powered router, there’s a major issue with this setup: if you’re not running a high-availability cluster, your entire Internet will go down any time your Proxmox home lab becomes unavailable. For DIY enthusiasts who love testing and breaking their home labs as much as I do, you’ll end up annoying your family if you configure the OPNsense/pfSense virtual machine on top of your main Proxmox system.
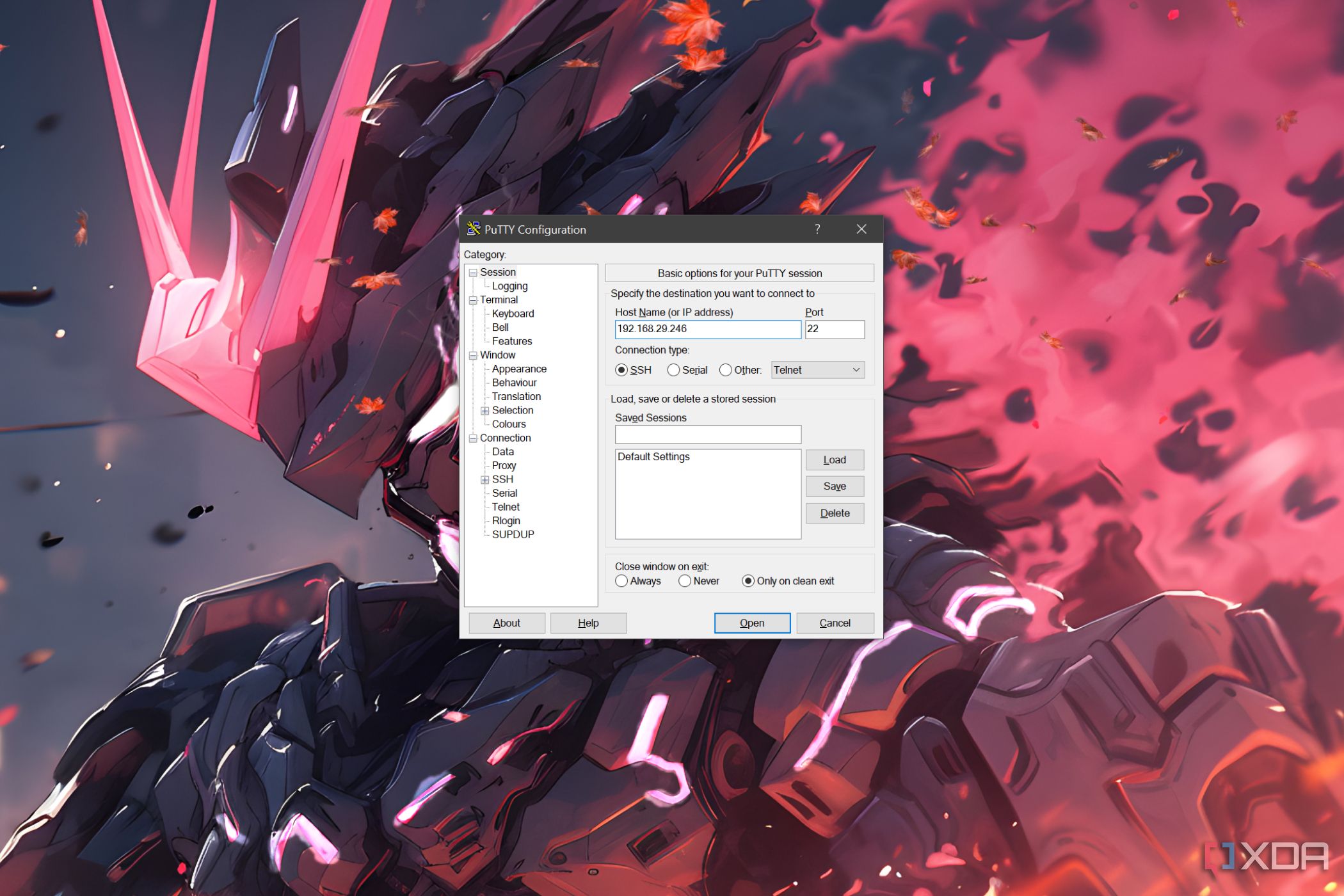
3 Harden the SSH protocol
By preventing root logins and setting up key authentication
Despite seeming rather overkill for a home lab setup, you can modify certain authentication rules for SSH if you’re anxious about hackers leveraging this protocol to run malicious scripts on your Proxmox machine. For instance, preventing root logins and limiting SSH access to other users is a great way to enhance the security of SSH connections.
Likewise, replacing the default SSH port (22) with a custom port can add an extra roadblock for unauthorized users trying to access the Proxmox. Replacing passwords with public keys can also help out, though doing so is a tad difficult for beginners.
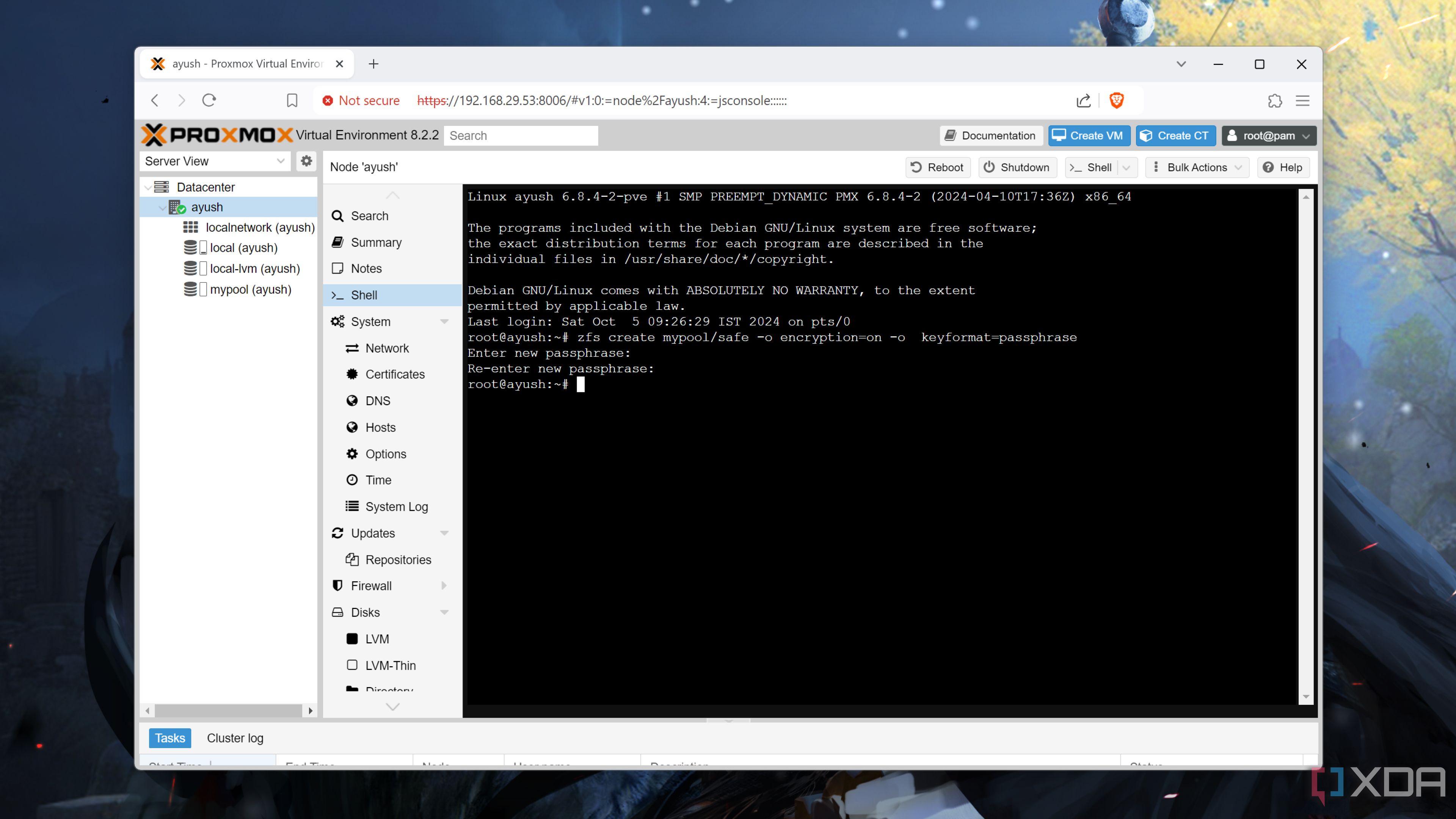
2 Encrypt ZFS disks
Quite useful for NAS setups with confidential data
Since Proxmox supports the ultra-useful ZFS file system, you can try encrypting the storage pools to prevent unauthorized physical access to the drives. There are a couple of ways to do so, but the easiest one involves using native ZFS encryption. Assuming you’ve already created a pool inside the ZFS tab of the Disks section, simply run the zfs create mypool/safe -o encryption=on -o keyformat=passphrase command and enter the Passkey of your choice to deploy an encrypted ZFS pool on Proxmox.
For the average user (myself included), encrypting the drives isn’t all that useful. However, if you’re storing sensitive information inside a Proxmox-turned-NAS server, there might be some value in setting up native ZFS encryption.
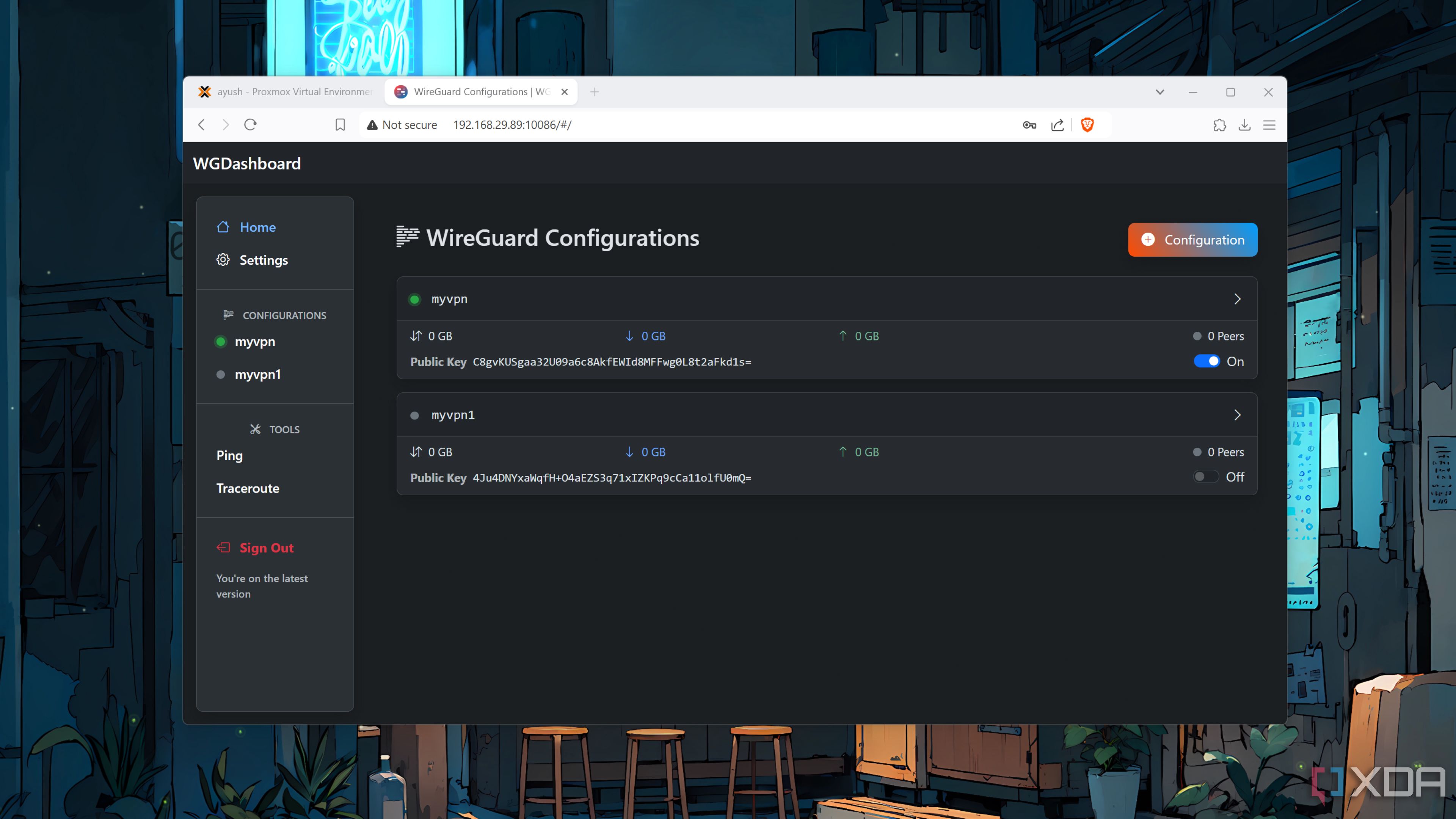
1 Never expose the host to devices outside your home network
And if you must, always go the VPN route
Just like your NAS server, it’s never a good idea to expose your private home lab to remote access over the Internet. If you’re a complete newcomer to the Proxmox landscape, I’d suggest keeping the Pandora’s Box called remote access closed for the time being.
In case your workflow demands remote access to your precious Proxmox server, I recommend using a VPN to use the host machine. There are several ways to do this, including paid VPN services and self-hosted WireGuard containers (with port forwarding enabled on your home router).
Keeping your Proxmox server safe and sound
So long as you follow most of these tips, you won’t have to worry about cybersecurity threats breaching your Proxmox server. In case you’re more concerned about drive failure rendering your VMs inaccessible, I recommend installing the Proxmox Backup Server ISO on a separate machine and linking it to your Proxmox node(s).
Once you’ve set up all the security features on your Proxmox machine, you can enjoy experimenting with the home lab to your heart’s content. Whether you’re looking for pragmatic things to do with Proxmox or just want to spend the weekend trying out some truly wacky home lab ideas, there are plenty of projects you can build with this virtualization platform.
#secure #Proxmox #home #lab
source: https://www.xda-developers.com/secure-proxmox-home-lab/